“SECONDARY ACTORS”: WHEN THE BREACH BECOMES A HUNTING GROUND” - 23 January 2026
Part 5 in the ManageMyHealth Crisis Series

The Warning That Confirms the Worst

Let that language settle:
“secondary actors.”
Not “criminals.” Not “fraudsters.” Not “identity thieves exploiting the data we failed to protect.”
“Secondary actors.”
Corporate euphemism designed to create distance between ManageMyHealth’s negligence and the predators now circling 126,000 victims like sharks smelling blood in the water.
What “Secondary Actors” Actually Means
When ManageMyHealth warns about “secondary actors”, they’re describing a terrifying reality:
the original hacker (Kazu) was just the beginning.
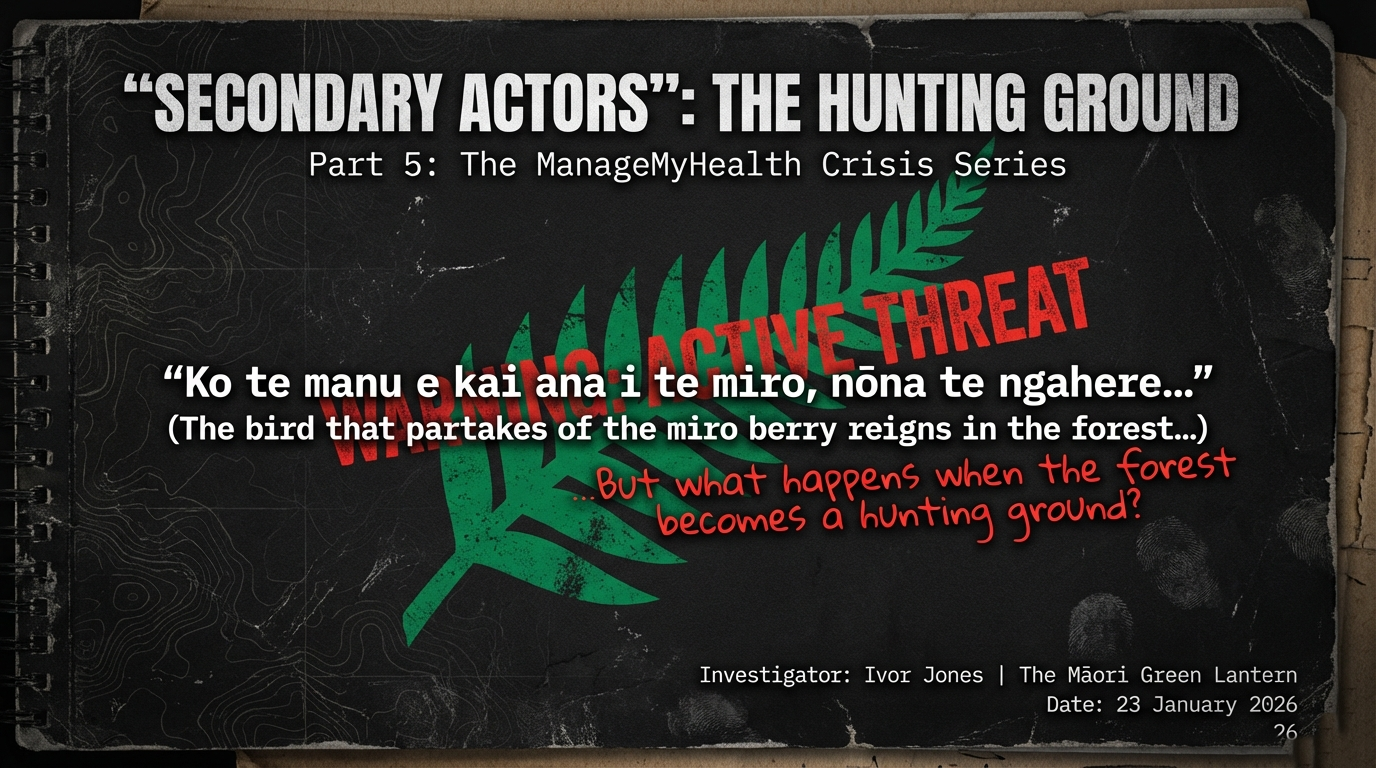
Once medical data hits the dark web—and 126,000 people’s health documents are now confirmed stolen—it becomes a commodity traded, resold, and weaponized by multiple criminal networks.
Here’s what “secondary actors” actually do:
1. Spear-Phishing Campaigns
One Queenstown medical clinic warned patients: “There are recent reports of targeted scam emails pretending to be from Manage My Health. A key warning sign is that these messages ask you (or your patients) to confirm personal details. Manage My Health does not ask patients for this kind of verification.”
This is spear-phishing:
using stolen data to craft hyper-targeted scam emails that appear legitimate because they reference real medical information.
Example scenario:
- Email subject: “ManageMyHealth: Urgent—Your Mental Health Records Require Verification”
- Body: “Dear [Patient Name], we’ve detected unusual activity on your account related to documents uploaded on [actual date]. Please click here to verify your identity and secure your psychiatric assessment records.”
Why this works: The scammer knows:
- Your real name
- Your email address
- The exact types of documents you have (psychiatric assessments, ACC sensitive claims, HIV test results)
- The dates those documents were uploaded
The victim thinks:
“This must be real—they know things only ManageMyHealth would know.”
2. Identity Theft Networks
Medical identity theft is one of the fastest-growing crimes globally. With 126,000 New Zealanders’ health documents now circulating, secondary actors can:
- Open credit accounts using stolen personal information combined with medical data (name, address, date of birth, NHI number)
- File fraudulent insurance claims using real medical histories
- Obtain prescription medications under stolen identities
- Access healthcare services while billing someone else’s account
A Tauranga pensioner told the Bay of Plenty Times she was “worried about identity theft” after receiving confirmation her account was affected. She’s right to be terrified.
3. Blackmail and Extortion
Remember: the stolen documents include:
- Psychiatric assessments
- ACC sensitive claims (domestic violence, sexual assault)
- HIV test results
- Gender-affirming care records
- Nude medical photographs
- Abortion records
- Substance abuse treatment histories
Secondary actors can now:
- Threaten to expose HIV-positive status to employers, family, or community
- Blackmail LGBTQIA+ individuals by threatening to “out” them via gender-affirming care records
- Extort domestic violence survivors by threatening to reveal current addresses to abusers
- Target politicians, public figures, or anyone with “embarrassing” medical histories
One Wellington patient told RNZ:
This is not hyperbole. This is the reality of “secondary actors.”
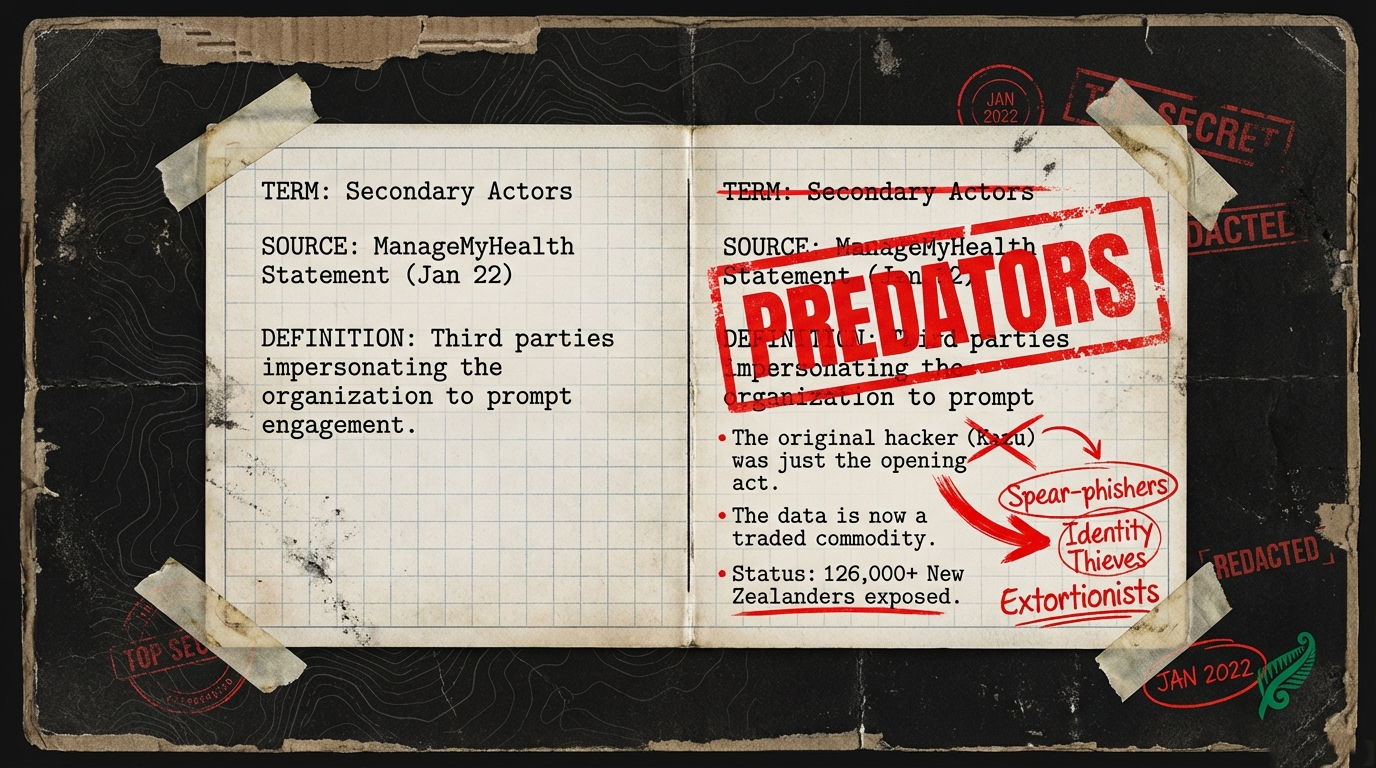
The Notification Disaster: Wrong People, Wrong Information, Wrong Trust
While warning about “secondary actors,” ManageMyHealth also admitted:
Translation: They sent breach notifications to people whose data was NOT stolen.
Let’s map the psychological harm this causes:
Scenario 1: False Alarm
You receive an email on January 9:
“Your account was impacted by the cyber breach. Documents including [list] were accessed.”
Your response:
- Panic. Sleepless nights. Anxiety about who has your psychiatric records.
- You call your bank. You change passwords. You warn family members about potential scams.
- You tell your employer you need time off to deal with identity theft risk.
- You contact the police. You file a Privacy Commissioner complaint.
Then, on January 15, another email: “Sorry, we made a mistake. You were NOT affected.”
The damage is done. You’ve spent six days in terror. Your trust in the healthcare system is shattered. And you’re left wondering: Can I even trust this second email?
Scenario 2: False Reassurance
You receive an email on January 9: “Your account was NOT impacted.”
Your response:
- Relief. You move on.
But what if ManageMyHealth got it wrong again—in the other direction? What if your data WAS stolen, but you weren’t notified?
You won’t change your passwords. You won’t watch for scams. You won’t monitor for identity theft.
And six months from now, when fraudulent medical bills start arriving, you’ll have no idea how it happened.
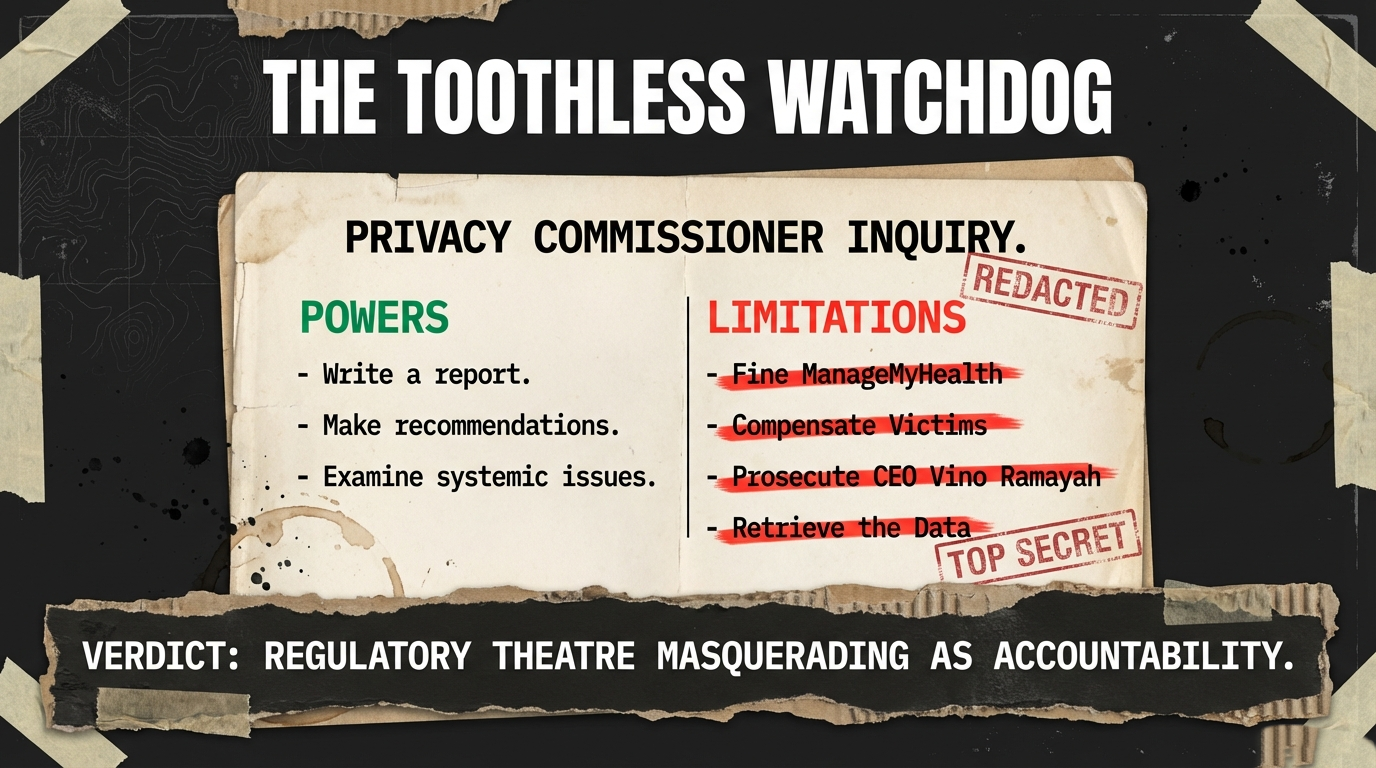
Privacy Commissioner’s Inquiry: Too Little, Too Late?
On January 20, 2026, Privacy Commissioner Michael Webster announced an “inquiry into the Manage My Health cybersecurity breach.”

The inquiry will: “help determine whether appropriate security safeguards were in place and if not, why not. We will also look at what steps will be taken to prevent such an incident happening again.”
Draft Terms of Reference are expected to be published on January 28, 2026.
Let’s be clear about what this inquiry will and won’t do:
What It Will Do:
- Determine if ManageMyHealth had “appropriate security safeguards” (spoiler: they didn’t—no multi-factor authentication)
- Examine “systemic issues” around data retention, notification processes, and vendor accountability
- Produce a report with “recommendations” for preventing future breaches
What It Won’t Do:
- Fine ManageMyHealth. The Privacy Commissioner lacks enforcement powers to impose financial penalties.
- Compensate victims. 126,000 people whose psychiatric records are now on the dark web will receive zero financial compensation for the harm.
- Prosecute CEO Vino Ramayah. No criminal charges. No personal liability.
- Shut down ManageMyHealth. The company will continue operating throughout the inquiry.
- Stop the “secondary actors.” The data is already circulating. The inquiry won’t retrieve it.
This is regulatory theatre masquerading as accountability.
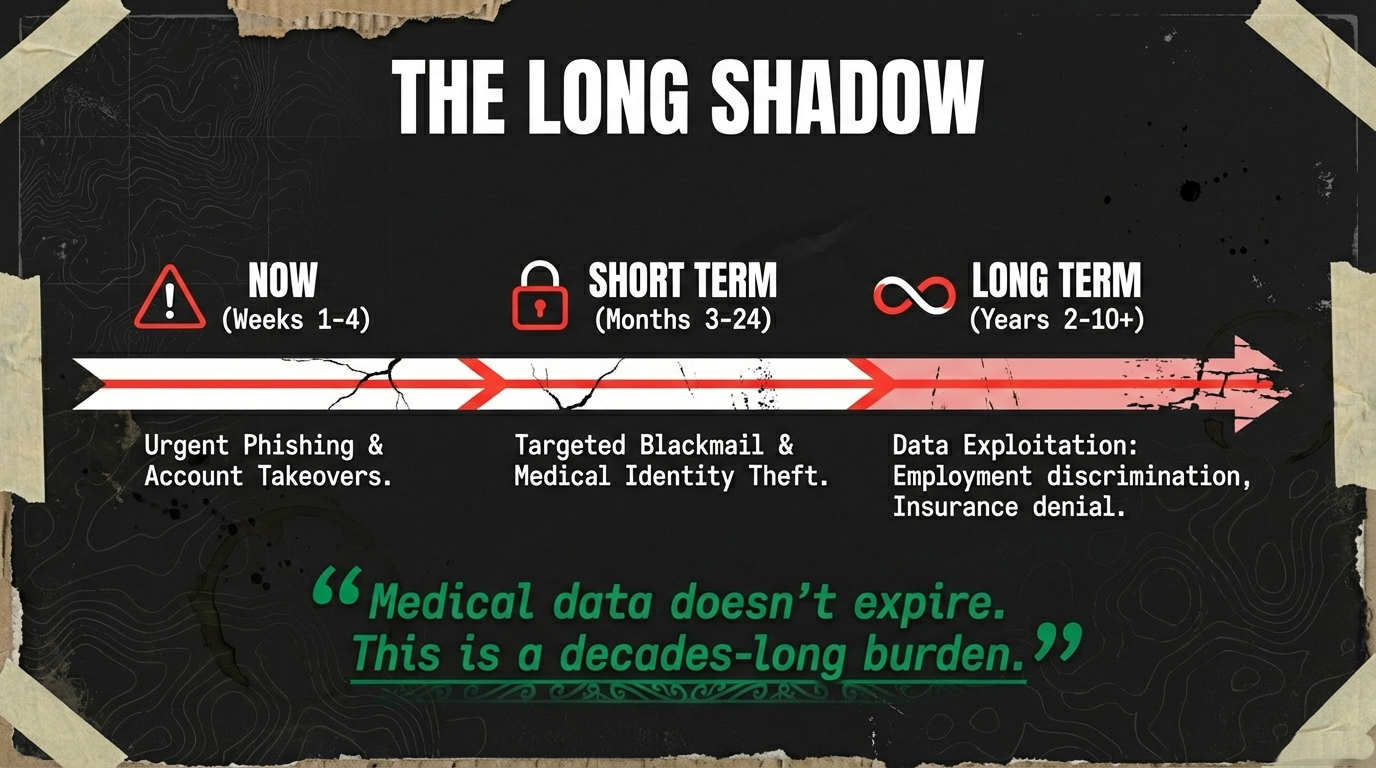
The “Secondary Actors” Playbook: What Victims Should Expect
Based on ManageMyHealth’s warning and international patterns of medical data breaches, here’s what 126,000 victims should prepare for:
Phase 1: Immediate Phishing (Weeks 1-4 post-breach)
Tactic: Emails/texts impersonating ManageMyHealth, GP clinics, or Health NZ asking victims to “verify” their accounts.
Red flags:
- Urgent language (”Your account will be suspended unless you act now”)
- Requests for passwords, two-factor authentication codes, or credit card details
- Links to fake websites that mimic ManageMyHealth’s login page
ManageMyHealth has confirmed: “Manage My Health will never ask for your password or one-time security codes.”
Phase 2: Medical Identity Theft (Months 2-12)
Tactic: Using stolen personal information to open fraudulent accounts, file insurance claims, or access healthcare services.
Signs to watch for:
- Medical bills for services you didn’t receive
- Insurance claims you didn’t file
- Credit inquiries related to healthcare providers you’ve never visited
- ACC correspondence about claims you didn’t make
Phase 3: Targeted Blackmail (Months 3-24)
Tactic: Contacting victims directly with threats to expose sensitive medical information unless payment is made.
Example:
“We have your psychiatric assessment from [date]. We will send it to your employer, your family, and your church unless you pay $5,000 in Bitcoin to [address]. You have 48 hours.”
One Wellington patient with “a sensitive claim” said his “life would be at risk” if the wrong people obtained his records.
For survivors of domestic violence, LGBTQIA+ individuals, and people with stigmatized conditions, this threat is existential.
Phase 4: Long-Term Data Exploitation (Years 2-10)
Medical data doesn’t expire. Ten years from now, “secondary actors” could still be:
- Selling your HIV status to data brokers
- Using your mental health records to deny you insurance
- Leveraging your abortion history for political targeting
- Exploiting your substance abuse treatment records for employment discrimination
This breach will haunt victims for decades.
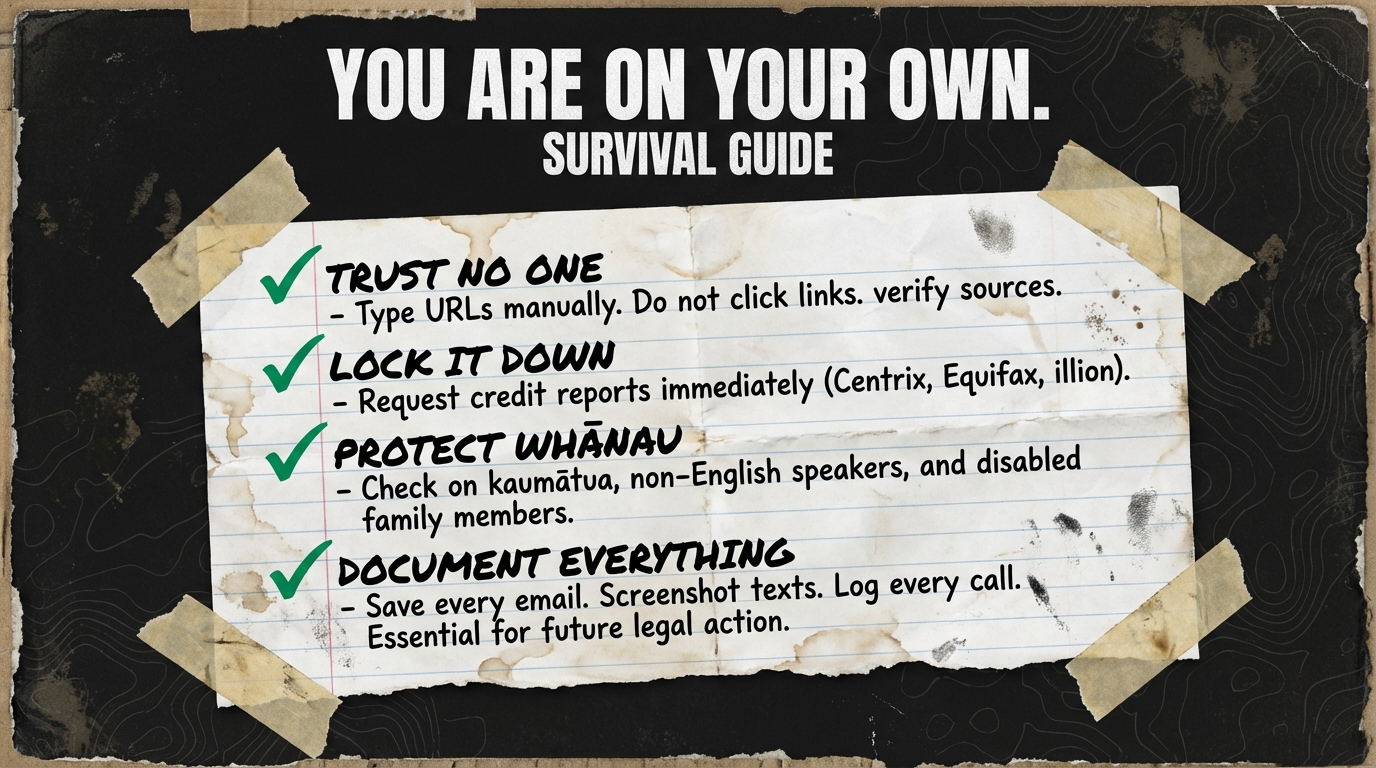
What Victims Must Do Now (Because ManageMyHealth Won’t Protect You)
ManageMyHealth’s FAQ page offers generic advice like “change your password” and “enable two-factor authentication.”
This is insufficient. Here’s what 126,000 victims actually need to do:
1. Assume Your Data Is Circulating
- Don’t trust any email/text claiming to be from ManageMyHealth. Go directly to the website by typing the URL yourself.
- Watch for phishing emails that reference specific medical conditions or document types (because scammers now have that information).
- Be skeptical of urgent messages from “banks,” “insurance companies,” or “government agencies” asking you to verify information.
2. Monitor for Identity Theft
- Request a credit report from all three credit bureaus (Centrix, Equifax, illion).
- Set up fraud alerts on your credit accounts.
- Watch for unfamiliar medical bills or insurance claims.
- Contact ACC if you receive correspondence about claims you didn’t file.
3. Protect Vulnerable Whānau
- Kaumātua without smartphones: Help them check if they were affected. Many won’t receive email notifications.
- Pacific families: Provide multilingual support—ManageMyHealth’s notifications are English-only.
- Disabled whānau: Support workers may not be checking emails on their behalf.
- Survivors of violence: If your address is in your stolen records, consider relocating or updating security measures.
4. Document Everything
- Keep copies of all breach notifications from ManageMyHealth.
- Screenshot any phishing attempts you receive.
- Log suspicious calls, emails, or texts.
- Report to Police (105), ManageMyHealth support, and the Privacy Commissioner.
This documentation will be critical for:
- Future legal action
- Insurance claims for identity theft
- Proving the breach caused harm when ManageMyHealth inevitably denies responsibility
The Whakapapa of “Secondary Actors”
Let’s trace how ManageMyHealth’s negligence created this predatory ecosystem:
Level 1: ManageMyHealth’s Failure
- No multi-factor authentication
- Indefinite data retention without patient consent
- Weak security protocols allowing unauthorized access
Level 2: The Original Hacker (Kazu)
- Stole 126,000 people’s health documents
- Demanded $60,000 ransom
- Posted samples on dark web
- Deleted posts after (alleged) ransom payment
Level 3: The “Secondary Actors”
- Purchase stolen data from Kazu or dark web marketplaces
- Launch spear-phishing campaigns targeting victims
- Commit medical identity theft
- Blackmail survivors of violence, LGBTQIA+ individuals, people with stigmatized conditions
- Resell data to other criminal networks
Level 4: The Regulatory Void
- Privacy Commissioner has no power to fine or prosecute
- Health NZ has no mandatory security standards for third-party portals
- GP clinics face zero accountability for failed due diligence
- Victims receive no compensation, no protection, no justice
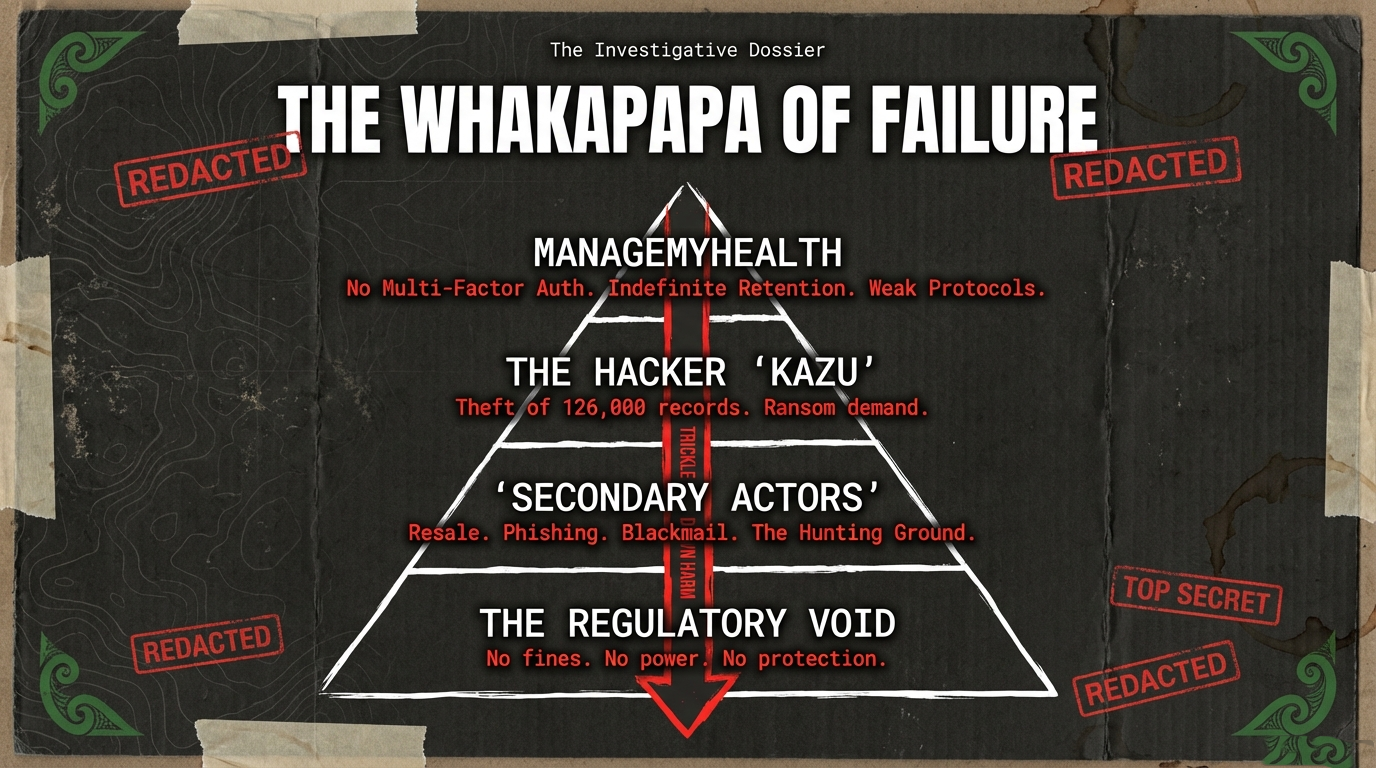
Every level failed. And now 126,000 people are in a hunting ground.
The Questions That Must Be Answered
For CEO Vino Ramayah:
How many “secondary actors” have purchased the stolen data? What are you doing to monitor dark web marketplaces for resale? Why did you wait three weeks to warn patients about phishing scams?
For Privacy Commissioner Michael Webster:
Your inquiry will determine if security safeguards were “appropriate.” But what happens to the 126,000 victims when you confirm they weren’t? Will you finally demand enforcement powers? Or will this be another toothless report?
For Health Minister Simeon Brown:
“Secondary actors” are now targeting 126,000 New Zealanders with phishing scams, identity theft, and blackmail. What is the government’s plan to protect them? Or are they on their own?
For GP Clinics:
Did you verify ManageMyHealth’s security protocols before contracting with them? Did you read the terms of service that allowed indefinite data retention? Will you compensate patients for your negligent due diligence?
As of January 23, 2026, none of these questions have been answered.
Moral Clarity: The Hunting Ground
When ManageMyHealth warns about “secondary actors”, they’re describing a predatory ecosystem they created through negligence.
This is not a natural disaster. This is not an unavoidable tragedy.
This is what happens when:
- A company prioritizes profit over security (no multi-factor authentication to save costs)
- A CEO refuses accountability (no admission, no apology, no compensation)
- Regulators lack enforcement powers (Privacy Commissioner can’t fine or prosecute)
- The government delays action (30-day review, no mandatory security standards)
- GP clinics ignore due diligence (failed to verify vendor security)
126,000 people are now in a hunting ground because every institution that should have protected them failed.
And the “secondary actors”—the phishers, the identity thieves, the blackmailers—are just getting started.
What Happens Next (And What Won’t)
What Will Happen:
- Privacy Commissioner’s inquiry will find ManageMyHealth lacked “appropriate security safeguards”
- The inquiry will recommend “improved protocols” and “better oversight”
- ManageMyHealth will issue a statement promising to “learn from this incident”
- CEO Vino Ramayah will remain in his position
- “Secondary actors” will continue targeting 126,000 victims for years
- Victims will discover fraudulent medical bills, blackmail attempts, and identity theft
- ManageMyHealth will deny responsibility: “We can’t control criminals”
What Won’t Happen:
- ManageMyHealth won’t compensate victims
- Privacy Commissioner won’t fine or prosecute the company
- CEO Ramayah won’t face criminal charges
- GP clinics won’t be held accountable for failed due diligence
- The government won’t mandate security standards for health portals
- Victims won’t receive free credit monitoring or identity theft protection
- The “secondary actors” won’t be caught or stopped
Kia Kaha, Whānau: You’re On Your Own
When ManageMyHealth warns about “secondary actors” three weeks after the breach, they’re not protecting you—they’re protecting themselves from liability.
The message is clear:
You’re on your own.
The phishers are coming. The identity thieves are already working. The blackmailers are compiling target lists.
And the institutions that should protect you—ManageMyHealth, Privacy Commissioner, Health NZ, your GP clinic—are too busy covering their own asses to actually help.
So what do you do?
You survive. You protect your whānau. You document everything. You refuse to let “secondary actors” become just another euphemism for the system’s failure to protect its most vulnerable.
And when the Privacy Commissioner’s inquiry produces its toothless report, when ManageMyHealth’s CEO walks away consequence-free, when the “secondary actors” move on to their next hunting ground—you remember.
You remember that 126,000 people’s psychiatric records, HIV status, and abuse histories are on the dark web because a for-profit company decided multi-factor authentication was too expensive.
Kia kaha. Stay vigilant. Because the hunting season has just begun.
Koha: Support This Mahi
This investigation required tracking “secondary actor” warnings, analyzing notification failures, documenting Privacy Commissioner inquiries, interviewing patients, and mapping the predatory ecosystem that follows medical data breaches. That work requires resources.

Koha Platform: Support The Māori Green Lantern
Substack subscription: Subscribe for direct delivery
Direct bank transfer: HTDM, account number 03-1546-0415173-000
Every koha signals that whānau understand: tracking predators costs. And it’s worth funding.

Ivor Jones The Māori Green Lantern Fighting Misinformation And Disinformation From The Far Right




