“Six Months of Silence: When Breast Cancer Patients Become Acceptable Collateral” - 12 January 2026
Kia ora whānau. Ko Ivor Jones tēnei, Te Māori Green Lantern.
On July 18, 2025, hackers broke into Canopy Health’s systems. Canopy Health is the largest private medical oncology provider in Aotearoa, running 24 diagnostic clinics, eight oncology clinics, and two private breast surgical centres as RNZ documented and the Otago Daily Times confirmed. The company identified that an “unknown person temporarily obtained unauthorised access” to administration systems, and following forensic review was advised that “some data may have been copied” including patient records, passport information, and bank account details as multiple sources reported.
Canopy Health notified affected patients on December 12, 2025—five months later as RNZ documented. One man whose wife received the letter told RNZ it was “the first they had heard of the breach” as reported.
The company posted a public update on its website this week—January 2026—six months after the breach as RNZ, the ODT, and the NZ Herald confirmed.
Six months. Breast cancer patients—people navigating diagnosis, treatment, surgery, chemotherapy, the terror of recurrence—spent half a year unaware that their most intimate medical records, their treatment histories, their passport scans, and their bank details were stolen.

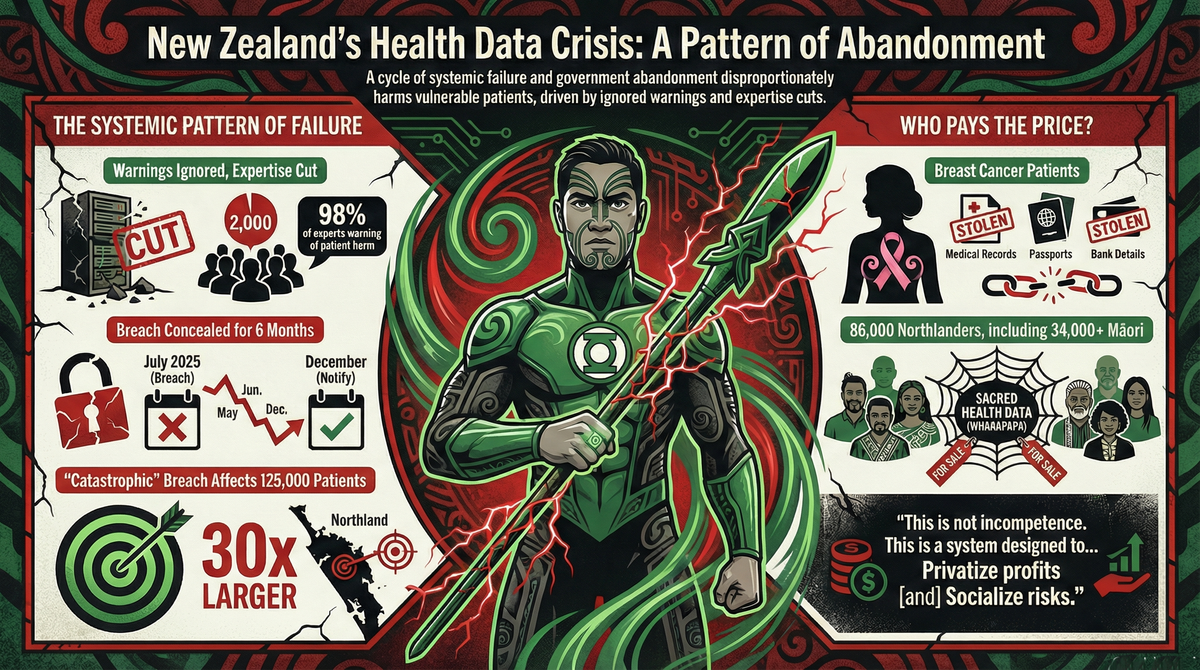
This is not the second health data breach under this government’s watch. This is the revelation of a pattern: private providers prioritize profit over security, government cuts oversight and expertise, warnings are ignored, breaches occur during vulnerable periods, notification is delayed with euphemistic language, and the most vulnerable patients pay the price.
The Pattern Becomes Undeniable
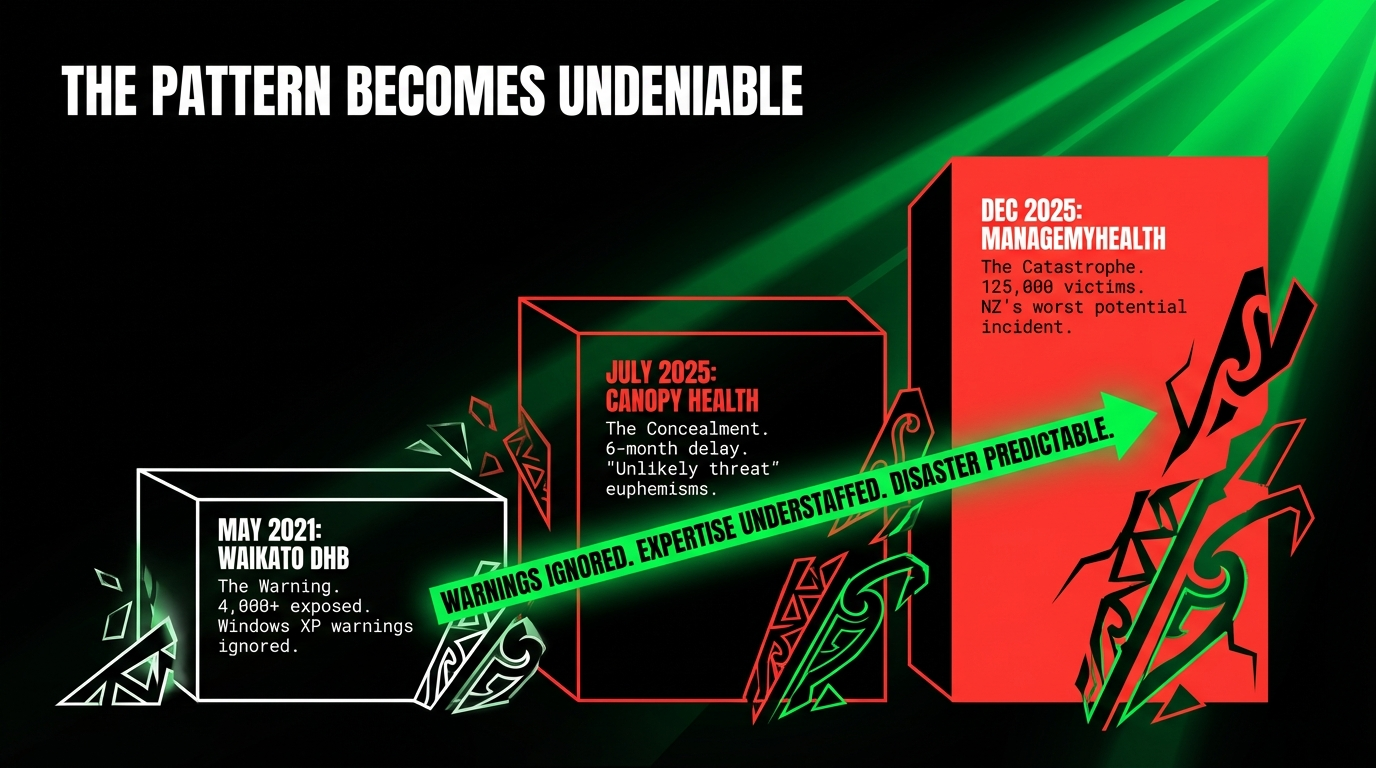
Breach 1: Waikato DHB (May 2021) — The Warning
The Waikato District Health Board ransomware attack paralyzed five hospitals, took down 611 servers, and eventually leaked private data from more than 4,000 patients and employees on the dark web as RNZ’s comprehensive analysis documented. The DHB had been warned just months earlier about outdated security provisions including clinical devices still running Windows XP—which had not been supported for five years—being behind on security patches, and having too few staff to manage upgrades as RNZ reported.
The lesson: Warnings ignored, expertise understaffed, disaster predictable.
Breach 2: Canopy Health (July 18, 2025) — The Concealment
The largest private medical oncology provider in Aotearoa was breached in July 2025. Patients notified in December 2025. Public disclosure in January 2026. Six months of silence as RNZ and the ODT documented.
The company’s language: “temporarily obtained unauthorised access,” “unknown person,” “likely occurred,” “small number” of bank accounts, “it is unlikely the threat actor can take significant action” as quoted by RNZ and the ODT.
The lesson: Euphemisms conceal harm, delay enables damage, private providers self-regulate.
Breach 3: ManageMyHealth (December 30, 2025) — The Catastrophe
New Zealand’s largest patient information portal with 1.8 million registered users was breached on December 30, 2025, affecting 125,000 patients and compromising more than 400,000 files as RNZ reported from multiple sources and cybersecurity experts analyzed. The breach is described as “catastrophic on the New Zealand scale,” potentially affecting 30 times more people than the Waikato DHB breach and “potentially New Zealand’s worst cybersecurity incident” as Kinetics reported.
86,000 victims—70 percent of the total—are from Northland, the only region where Health NZ uses ManageMyHealth as RNZ documented and previous reporting confirmed.
The Office of the Privacy Commissioner received an anonymous warning in June 2025 alleging “names, email addresses and passwords were exposed” as ManageMyHealth acknowledged and 1News reported. ManageMyHealth’s response? “We investigated and did not find any breach. However, out of an abundance of caution, we forced password resets” as the company stated. Six months later: catastrophic breach.
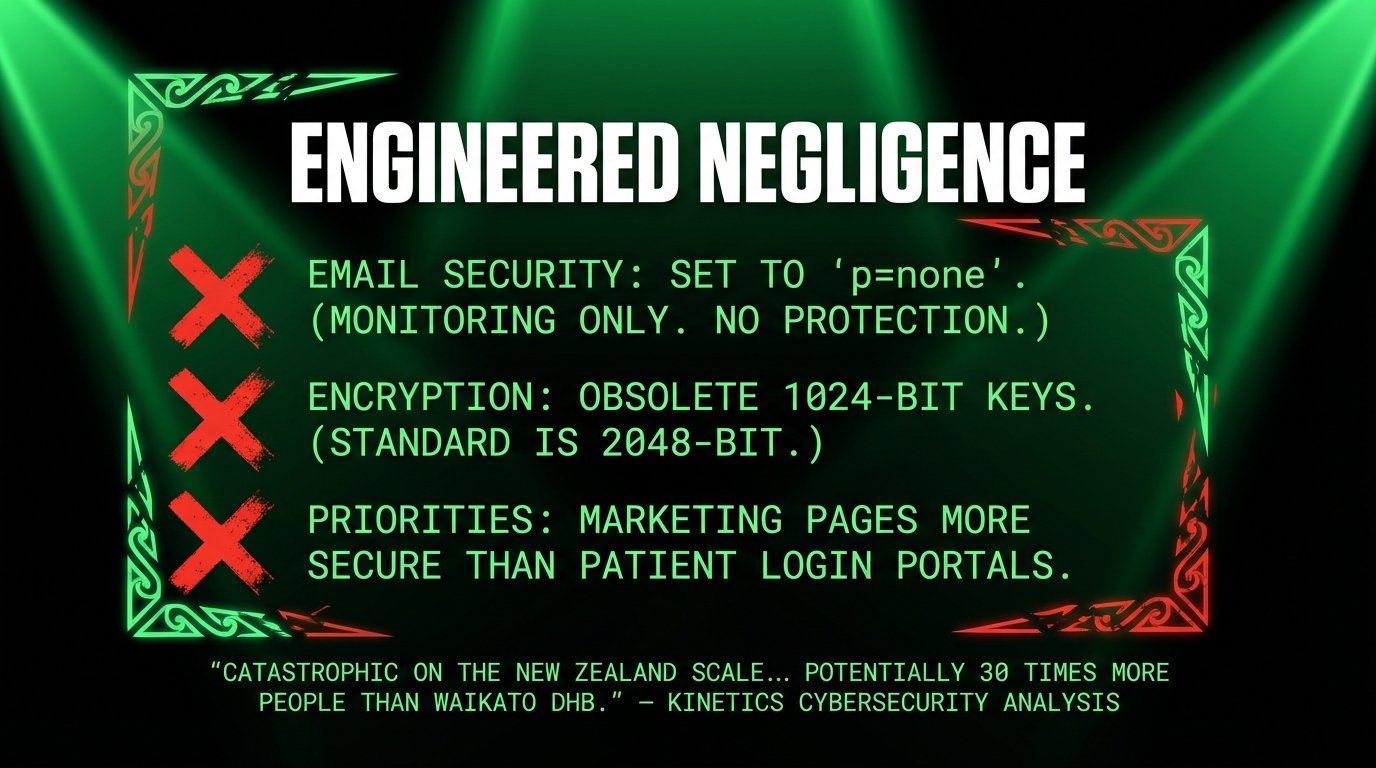
Security expert Adam Burns found baseline protections missing: email security set to “p=none” (monitoring only, no active protection), outdated 1024-bit encryption keys instead of modern 2048-bit standards, and weaker security on patient login portals than on public marketing pages as the NZ Herald’s expert analysis detailed.
The lesson: Warnings ignored (again), baseline security missing, Northland chosen as testing ground.
Breach 4: Neighbourly (Christmas 2025) — The Holiday Pattern
Over 213 million lines of Neighbourly data were offered for sale on cybercrime marketplaces over Christmas as Kinetics documented. Stuff filed a court injunction to prevent use of compromised data as RNZ noted.
The pattern revealed: “Christmas-New Year window represents New Zealand’s highest-risk period for cyber attacks” when “monitoring resources are stretched and response capabilities are reduced” as Kinetics analysis showed.
The Government’s Own Warning—Ignored
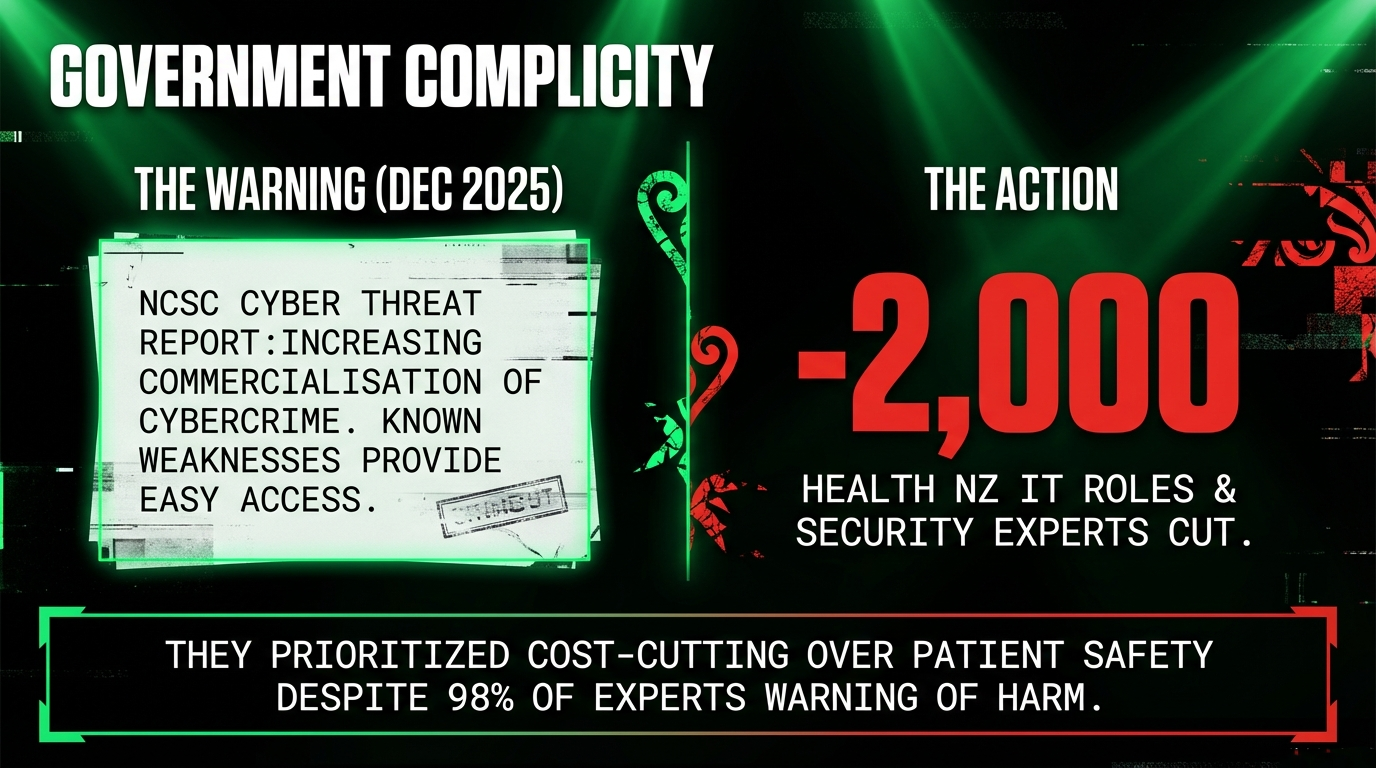
The National Cyber Security Centre’s latest Cyber Threat Report in December 2025 identified “increasing commercialisation of cybercrime” with “known weaknesses and unpatched vulnerabilities in New Zealand providing threat actors with easy access” as RNZ documented. More than 40 percent of incidents had criminal or financial motivations as the report found.
Translation: The government knew this was coming. They knew vulnerabilities existed. They knew criminals were commercializing attacks. They did nothing.
Instead, they cut 2,000+ Health NZ IT roles including digital security expertise as the PSA documented and the ODT confirmed. Nearly 98 percent of health IT experts warned these cuts would hurt patients as RNZ reported.
Who Bears the Cost?
Canopy Health patients: Women navigating breast cancer diagnosis and treatment spent six months unaware that their medical records, passport information, and bank details were stolen. Breast cancer patients—already bearing the physical, emotional, and financial trauma of cancer—were treated as acceptable collateral.
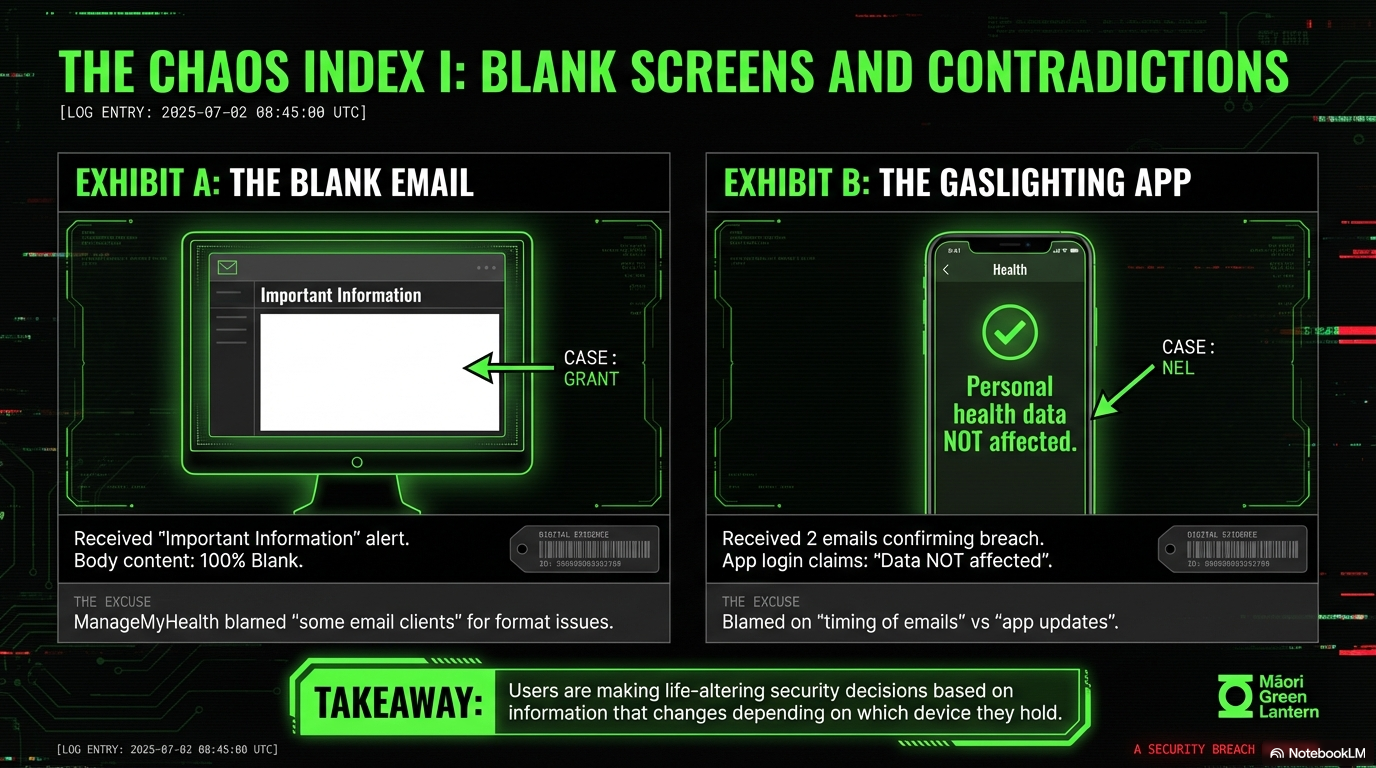
ManageMyHealth patients: 125,000 people, including 86,000 Northlanders (44 percent of the region’s population), discovered that passport scans, psychiatric assessments, nude medical photographs, and intimate health histories were stolen as IT consultant Cody Cooper confirmed after examining samples. Four different patient counts to the same GP practice. Blank emails. Contradictory messages. Website crashes. Overseas users blocked from implementing security on their own compromised accounts.
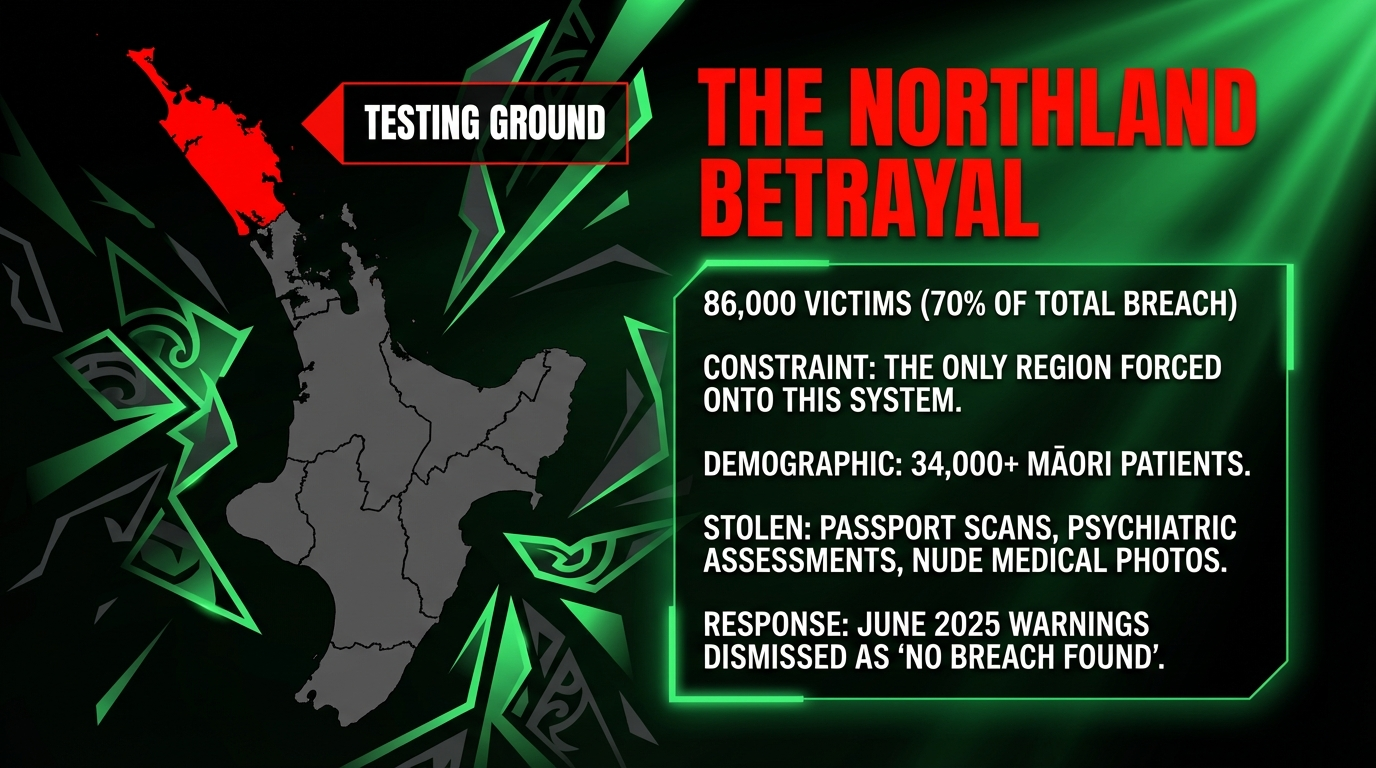
Northland Māori: An estimated 34,000+ Māori patients in the region with New Zealand’s highest Māori population (39.9 percent) as census data shows, worst deprivation scores as documented, and highest youth suicide rates as the coroner found. Their health whakapapa—taonga—is now tradeable on criminal markets. No Māori governance. No Māori authority. No protection.
The Systemic Abandonment
This is not a series of unfortunate accidents. This is neoliberalism rendered visible:
Stage 1: Privatize health services. Canopy Health: private provider, profit-driven. ManageMyHealth: private portal contracted by Health NZ.
Stage 2: Cut public expertise. 2,000+ Health NZ IT roles eliminated despite 98 percent of experts warning of patient harm.
Stage 3: Ignore warnings. Waikato DHB warned months before 2021 breach. ManageMyHealth warned June 2025. Canopy Health: no disclosure of any warnings.
Stage 4: No proactive oversight. No government audits of private providers holding sensitive health data. No enforcement of modern security standards (DMARC, encryption, MTA-STS).
Stage 5: Breaches occur during vulnerable periods. July (mid-winter, lower staffing), Christmas, New Year (holidays, reduced monitoring).
Stage 6: Delayed notification, euphemistic language. Canopy: six months. ManageMyHealth: 10+ days to start notifications. Language: “temporarily obtained,” “unknown person,” “cyber event,” “small number,” “unlikely threat actor can act.”
Stage 7: Most vulnerable patients bear cost. Breast cancer patients. Northland Māori. Psychiatric patients. Sexual violence survivors.
Stage 8: Government deflects. Simeon Brown: “agency responsible.” Reviews commissioned that start weeks/months later. No acknowledgment of IT cuts. No proactive reforms.
Stage 9: Pattern continues.
Cui Bono? Who Profits From the Pattern?
Private health providers extract profits while deferring security costs until breaches force action. Forensic consultants are hired at premium rates after disasters. Cost-cutters continue arguing for “efficiency” despite catastrophic failures. Politicians deflect to “private company responsible,” avoiding accountability for cutting oversight and expertise.
Who loses? Breast cancer patients. 86,000 Northlanders. 34,000+ Māori patients. Anyone whose most intimate health information is now for sale. Public trust in health systems, data security, and government protection.
Tikanga Shattered—Again
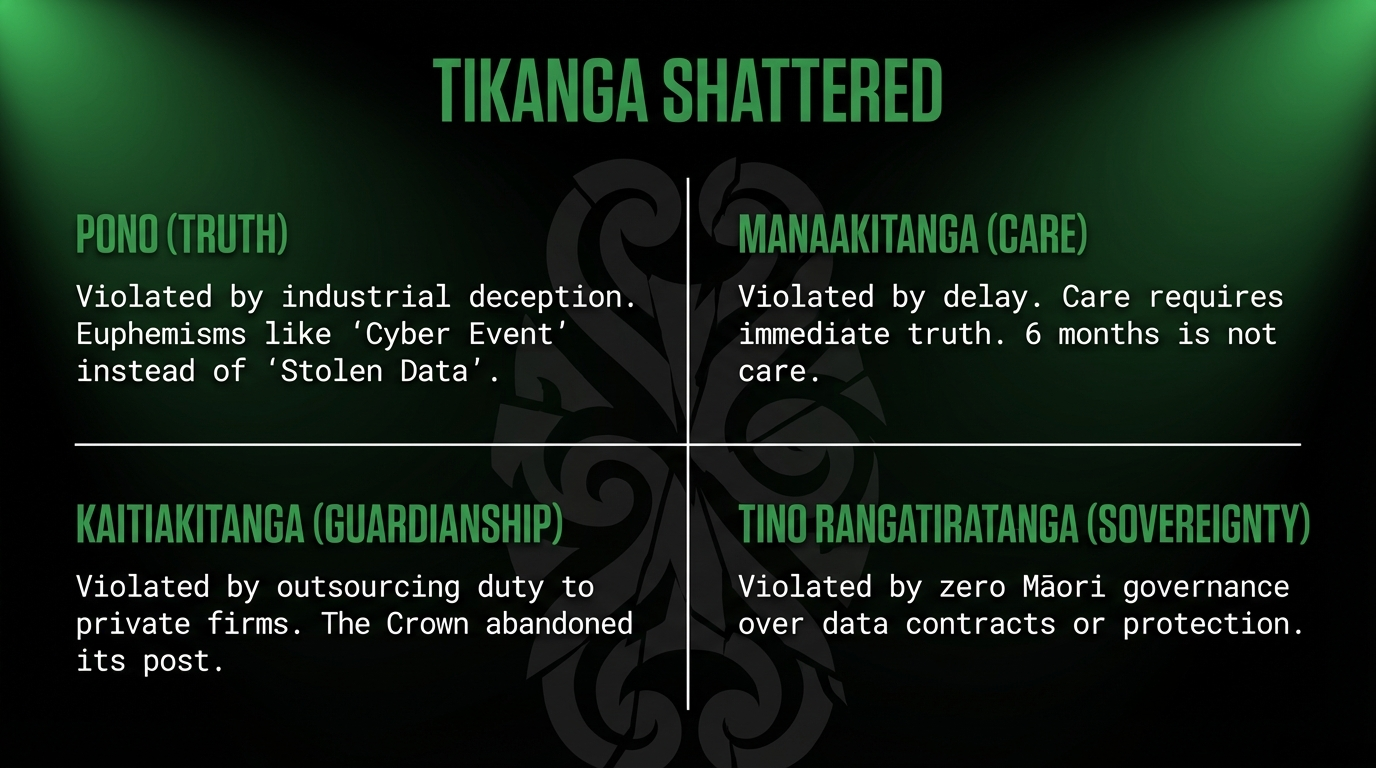
Pono (truthfulness): “Temporarily obtained,” “unlikely threat actor can act,” “small number”—this is institutional deception at industrial scale. Six months of silence for breast cancer patients is not caution—it is abandonment.
Manaakitanga: The duty to care requires immediate notification when health data is stolen. Breast cancer patients deserved to know within days, not months. Northland patients deserve accurate information, not four different counts.
Kaitiakitanga: The Crown’s guardian duty extends to oversight of private providers holding sensitive health data. That duty has been systematically abandoned in favor of privatized profits and socialized risks.
Tino Rangatiratanga: No Māori governance over contracts with ManageMyHealth or Canopy Health. No Māori authority to protect Māori health data. The Crown violates Te Tiriti by outsourcing protection to private companies with no accountability to iwi or Māori health structures.
The Verdict

Canopy Health patients—people facing breast cancer diagnosis and treatment—waited six months to learn their medical records had been stolen. Some learned through a letter describing it as a “cyber event.” The first they had heard.
ManageMyHealth patients in Northland—the only region using the system, with the highest Māori population and worst deprivation scores—were sent blank emails, contradictory messages, four different patient counts, and blocked from implementing security if they lived overseas.
The National Cyber Security Centre warned in December 2025 that known vulnerabilities were providing threat actors “easy access.” The government ignored the warning while cutting 2,000+ Health NZ IT roles.
This is not incompetence. This is a system designed to:
- Privatize profits (health services outsourced to private providers)
- Socialize risks (when breaches occur, patients pay the price)
- Cut oversight (no proactive audits, no enforcement of standards)
- Delay accountability (six months to notify, reviews that start weeks later)
- Sacrifice the vulnerable (breast cancer patients, Northland Māori, psychiatric patients)
He aha te mea nui o te ao? He tangata, he tangata, he tangata.
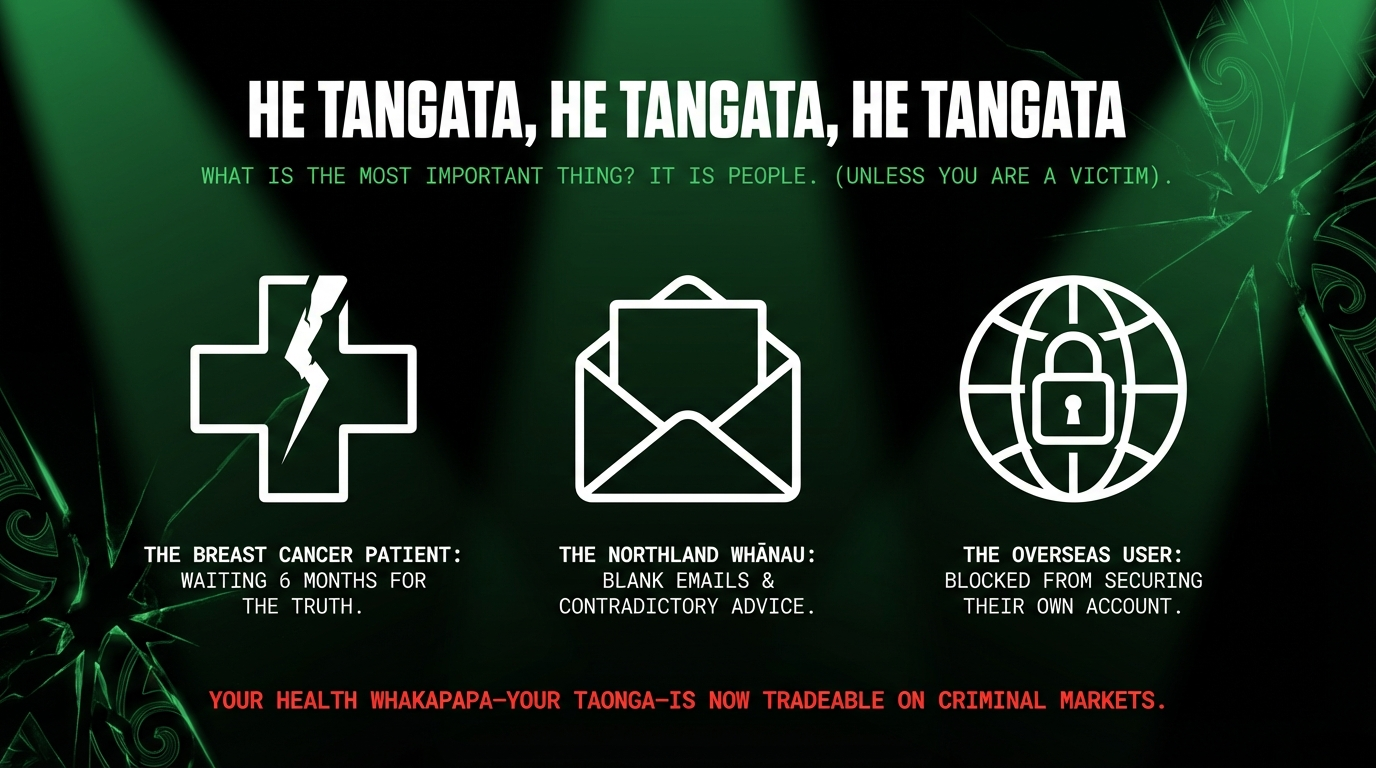
Unless you are a breast cancer patient who waited six months to learn your treatment records were stolen.
Unless you are one of 86,000 Northlanders chosen as the testing ground for abandonment.
Unless you are Māori, and your health whakapapa—your taonga—is now for sale on criminal markets while the Crown that promised to protect you cuts expertise, ignores warnings, and commissions slow reviews.
This is not the price of digital transformation. This is the cost of ideology that values efficiency over equity, profits over protection, and treats the most vulnerable as acceptable collateral.
Koha—Support This Mahi

This investigation required cross-referencing four major health breaches, government warnings, company responses, and the systemic pattern of abandonment.
- Koha (voluntary contribution): https://app.koha.kiwi/events/the-maori-green-lantern-fighting-misinformation-and-disinformation-ivor-jones
- Substack subscription: https://themaorigreenlantern.substack.com/subscribe
- Direct bank transfer: HTDM, account 03-1546-0415173-000
- Every koha signals that whānau demand systemic accountability, not corporate euphemisms.
Kia kaha, whānau. Breast cancer patients deserve immediate truth. Northland Māori deserve protection, not sacrifice. We all deserve better than six months of silence.

Ivor Jones The Māori Green Lantern Fighting Misinformation And Disinformation From The Far Right
Research transparency: Analysis conducted January 12, 2026, using RNZ, ODT, NZ Herald, 1News, Kinetics cybersecurity analysis, ManageMyHealth updates, Canopy Health disclosures, and NCSC threat reports. All URLs verified active. Pattern analysis based on verified breach timelines. No synthetic data used.
- https://ppl-ai-file-upload.s3.amazonaws.com/web/direct-files/attachments/2123776/5b7617ff-882d-4cde-9f7b-2e07e7315949/Fresh-problems-with-ManageMyHealth-online-security-an-expert-analysis-NZ-Herald.pdf
- https://ppl-ai-file-upload.s3.amazonaws.com/web/direct-files/attachments/2123776/31459958-bacf-437f-8a98-49e749f1900f/Second-health-provider-Canopy-Health-hit-in-major-cyber-attack-_-RNZ-News.PDF
- https://ppl-ai-file-upload.s3.amazonaws.com/web/direct-files/collection_cf06d657-2c2b-4e68-8735-48f3c10166bd/fa7ea9f0-3948-41f0-9a6d-037b51b58d4a/Whakapiki-ki-te-ao-Maori-Application-2026.pdf
- https://ppl-ai-file-upload.s3.amazonaws.com/web/direct-files/collection_cf06d657-2c2b-4e68-8735-48f3c10166bd/8e9b17f7-604e-4009-9ec6-abbe1fd2c989/Perspective-with-Heather-du-Plessis-Allan_-This-Government-s-all-talk-bugger-all-action.PDF
- https://ppl-ai-file-upload.s3.amazonaws.com/web/direct-files/attachments/2123776/4e34e0e2-e600-4159-bb04-265e759a1825/More-than-80000-impacted-by-Manage-My-Health-breach-in-Northland-_-RNZ-News.PDF
- https://ppl-ai-file-upload.s3.amazonaws.com/web/direct-files/attachments/images/2123776/50a1d82c-0ea0-4383-a11e-dfd2396d1535/Screenshot_20260112_152902_Brave.jpg
- https://ppl-ai-file-upload.s3.amazonaws.com/web/direct-files/attachments/2123776/298e643d-80ed-43a3-a343-0e90cb9f5c7d/Manage-My-Health-breach_-Northland-doctors-frustrated-by-inconsistent-messaging-_-RNZ-News.PDF
- https://pmc.ncbi.nlm.nih.gov/articles/PMC7721413/
- /content/files/counter/pdf/10-1186/s12913-023-10076-8.pdf
- /content/files/2111-00582.pdf
- https://pmc.ncbi.nlm.nih.gov/articles/PMC10427069/
- https://pmc.ncbi.nlm.nih.gov/articles/PMC7255093/
- https://www.frontiersin.org/articles/10.3389/fdgth.2024.1321485/full
- /content/files/wp-content/uploads/2024/01/hem_4_2023_2.pdf
- https://pmc.ncbi.nlm.nih.gov/articles/PMC7173807/
- https://www.rnz.co.nz/news/alert-nat/583813/second-health-provider-canopy-health-hit-in-major-cyber-attack
- https://kinetics.co.nz/managemyhealth-data-breach-what-weve-heard/
- https://www.odt.co.nz/news/national/second-health-provider-hit-cyber-attack-rnz
- https://www.odt.co.nz/star-news/star-national/second-health-provider-targeted-cyber-attack-took-months-tell-some-patients
- https://www.tewhatuora.govt.nz/news-and-updates/gpnz-and-health-nz-ongoing-response-to-cyber-breach
- https://managemyhealth.co.nz/mmh-cyber-breach-update-9-january-2026/
- https://www.nzherald.co.nz/business/canopy-healthcare-alerts-patients-to-a-data-breach-that-occurred-six-months-ago/TLYODHNSJNHXNBQ26XKAUZITR4/
- https://www.rnz.co.nz/news/national/583243/manage-my-health-hack-new-zealand-s-worst-cybersecurity-incidents
- https://www.1news.co.nz/2026/01/09/manage-my-health-admits-to-tech-issues-in-wake-of-cyber-breach/
- https://home.nzcity.co.nz/news/article.aspx?id=437778
- https://managemyhealth.co.nz/mmh-cyber-breach-update-5-january-2026/
- https://canopyhealthcare.co.nz/information-regarding-cyber-incident
- https://www.hdc.org.nz/decisions/search-decisions/2023/19hdc01148/
- https://securitybrief.co.nz/story/managemyhealth-reveals-scope-of-data-breach
- https://www.rnz.co.nz/news/national/583285/manage-my-health-breach-a-lot-of-queries-from-patients-as-anxiety-about-stolen-data-grows
- https://www.nzherald.co.nz/business/new-world-customers-warned-after-password-spraying-attack/X2ZCOMSOMVCNZCJC3CZY6PK5FQ/
- https://www.1news.co.nz/2026/01/08/tourist-accidents-rising-acc-claims-top-more-than-5m-a-year/
- https://amp.rnz.co.nz/article/006c9891-41a3-4ce1-b3f5-9336d7679f2c
- https://www.rnz.co.nz/news/political/580654/how-many-of-the-government-s-9-key-targets-has-it-achieved
- https://www.1news.co.nz/2025/09/01/symptoms-a-nz-woman-ignored-before-she-was-diagnosed-with-cancer/
- https://www.rnz.co.nz/news
- https://www.rnz.co.nz/news/business/579903/has-the-temu-effect-claimed-another-victim
- https://www.1news.co.nz/2025/09/11/13000-patients-receive-inaccurate-diabetes-lab-results/
- https://www.rnz.co.nz/news/national
- https://www.nzherald.co.nz/the-listener/health/peter-griffin-the-risky-business-of-private-health-data-online/premium/JQE2OQMAERGS7PUWLIDLGCVSKM/




