“The Earpiece Theory” - 28 September 2025
A Theoretical Analysis of an Alternative Assassination Method

Kia ora koutou katoa,
As a thought experiment, I wanted to examine the assassination of Charlie Kirk on September 10, 2025, at Utah Valley University, which has been officially attributed to Tyler Robinson, a lone gunman firing from the Losee Center rooftop approximately 430 feet away.

However, careful examination of the ballistic evidence, witness accounts, and video footage reveals significant inconsistencies that warrant exploration of an alternative theory. This essay examines the possibility that Kirk was killed not by a traditional sniper rifle, but through a sophisticated explosive device concealed within his security communication system—a method drawing disturbing parallels to the Israeli pager attacks on Hezbollah in Lebanon.
The Security Communication System Configuration
Kirk, as a high-profile conservative commentator, employed professional-grade security communications equipment during public appearances. Federal law enforcement protocols and private security details typically utilize two-wire surveillance systems for covert protection operations. These systems consist of an acoustic tube earpiece connected to a radio transmitter, with wiring that follows a specific routing pattern crucial to understanding the theoretical explosive placement.
According to standard surveillance earpiece configuration protocols, the system Kirk would have worn included: an earpiece positioned in his right ear, connected via clear acoustic tubing that wraps around the back of the ear for security. The primary wire harness runs from the radio unit, typically positioned on the left side of the body, up underneath clothing to maintain covert appearance. The microphone component, part of the two-wire system, routes across the torso from the radio position to optimize voice pickup while remaining concealed.
This routing creates a wire path that originates from the right ear, travels down the back of the neck, across the upper torso, and terminates at the radio unit positioned on the left side of the body—precisely the trajectory that would explain the wound pattern observed in the assassination.

The Ballistic Inconsistency and Wire-Based Explosive Theory
The foundation of this alternative theory rests on a fundamental ballistic contradiction that becomes explicable when considering the security wire routing. Kirk was wearing his communication earpiece in his right ear during the event, yet the documented exit wound appeared on the left side of his upper chest. For Robinson’s shot from the northeast rooftop position to create this wound pattern, the bullet trajectory would need to travel from right to left in a sharp downward angle—beginning at Kirk’s right ear and terminating at his left upper chest.
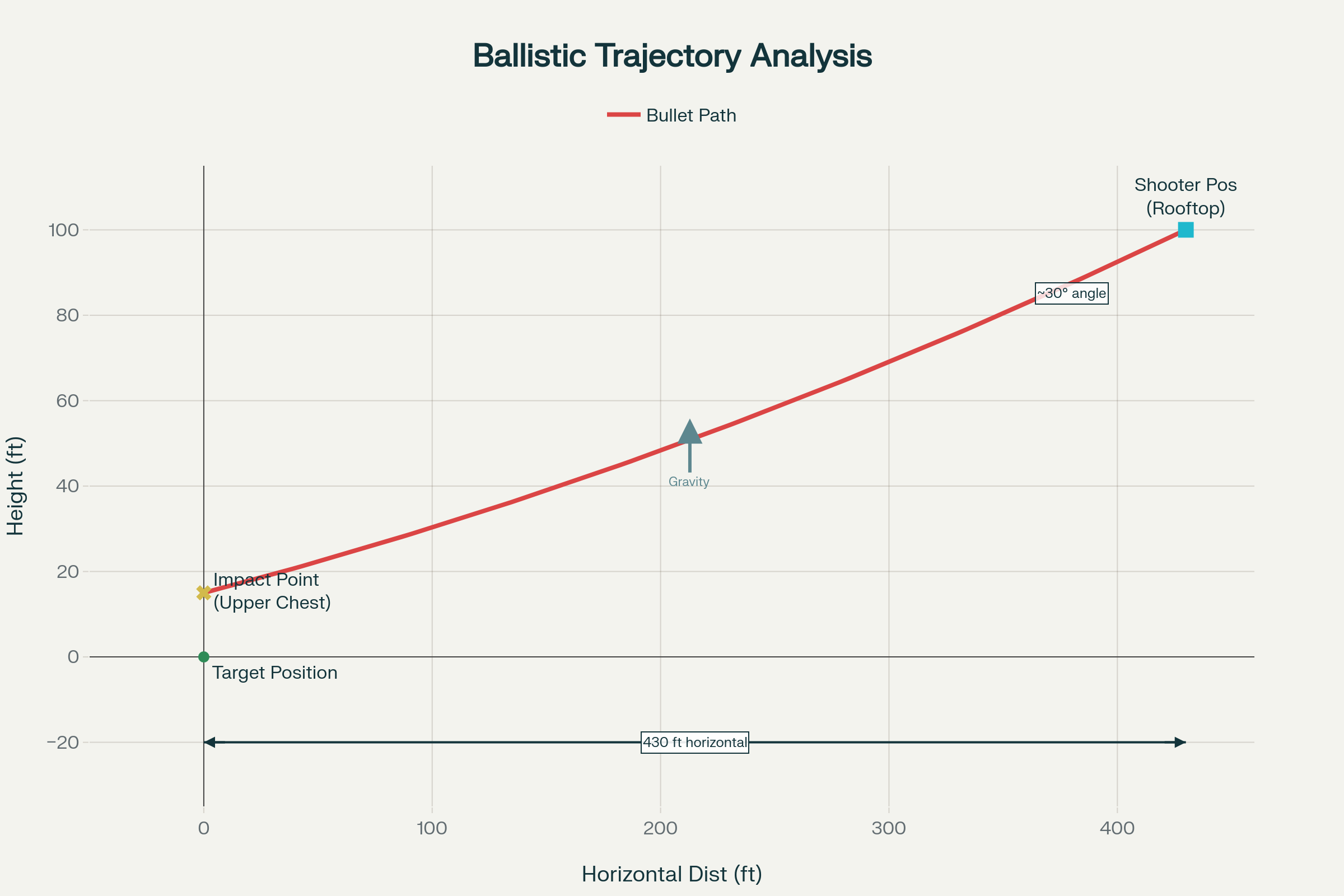
Official ballistic trajectory analysis showing the bullet path from the Losee Center rooftop to Charlie Kirk’s position, demonstrating the downward angle consistent with the documented evidence
However, the theoretical placement of an explosive device along the security wire harness provides a more plausible explanation for this trajectory. If a miniaturized explosive charge were positioned at the point where the wire system crosses from the back of the neck to the left side of the torso—following standard surveillance equipment routing —detonation would create an explosive force vector consistent with the observed wound pattern. The device would be positioned along the wire path running from Kirk’s right ear, across his upper back and shoulder, to the exit point at his left upper chest where the radio unit was positioned.
Historical Precedent: The Lebanese Pager Attacks
The September 2024 Israeli operation against Hezbollah provides a chilling template for this theoretical assassination method. Thousands of pagers and walkie-talkies simultaneously exploded across Lebanon, demonstrating several capabilities crucial to our scenario:
Supply Chain Infiltration: Israeli intelligence successfully intercepted and modified electronic devices during manufacturing, installing miniaturized explosive charges with detonators “invisible to X-ray” screening. The operation demonstrated sophisticated technical capability to weaponize everyday communication devices while maintaining their normal functionality until activation.
Remote Activation: Devices were triggered simultaneously by external signals, proving precise timing control over distributed explosive devices. The coordinated nature of the attacks showed advanced command and control capabilities essential for synchronized operations.
Surgical Precision: Explosions maximized damage to users while minimizing collateral casualties to nearby individuals. This precision targeting capability indicates sophisticated engineering of blast characteristics and directional explosive force.
Technological Sophistication: Advanced detonation mechanisms remained dormant for extended periods until activated by specific signals. The devices functioned normally for months before activation, demonstrating long-term operational security.

The Coordinated Operation Framework
Executing an earpiece-based assassination requires sophisticated multi-team coordination with military-grade precision timing, as evidenced by the FBI’s ongoing investigation into potential coordination and communication between multiple parties.
The Spotter: Positioned with visual confirmation of Kirk’s location, monitoring his exact movements and providing real-time intelligence to coordinate optimal activation timing while minimizing detection risks. The FBI has investigated viral video footage showing alleged hand signals from Kirk’s security team moments before the shooting.
The Audio Coordinator: Creates the auditory deception forming the backbone of investigative misdirection. At precisely 12:23:30 PM, triggers a gunshot sound effect creating acoustic evidence witnesses would report , establishing the false “sniper shot” narrative that multiple witnesses confirmed hearing.
The Device Operator: Controls remote detonation of the modified explosive device positioned along the security wire harness, requiring technical expertise in wireless protocols and microsecond timing to synchronize explosive activation with audio deception. This coordination would mirror the precision timing demonstrated in the Lebanese pager attacks.
The Decoy Coordinator: Pre-positions physical evidence on the rooftop supporting the sniper narrative, including the rifle, Robinson’s DNA samples, shell casings, and forensic evidence investigators would discover as “proof” of traditional assassination. Robinson’s confession note and pre-attack planning materials provide additional cover for the deception.
Fictional coordination method for movie plot showing synchronized audio and explosive elements with multiple team members
Technical Device Specifications and Wire Integration
The theoretical explosive device represents significant advancement in miniaturized explosive technology integrated with standard security communications equipment:
Explosive Charge Integration: Small but powerful explosive similar to pager attack devices , designed for maximum localized damage while maintaining normal wire harness appearance and communication functionality. The device would be positioned along the wire path where it crosses the upper torso, following standard surveillance equipment routing protocols.
Detonation System: Wireless receiver integrated into the communication system, detecting specific frequency signals or digital activation codes transmitted during the event. This enables remote triggering from safe distances while maintaining the cover of legitimate security equipment operation.
Concealment Design: Functions as legitimate communication wire harness while hiding lethal components from visual inspection and standard security screening. The device would appear as a standard component of professional security communications equipment, invisible to normal security protocols.
Directional Force Engineering: Engineered to create blast patterns following the wire path from right ear to left chest, specifically designed to produce exit wounds consistent with rifle trajectory while maximizing internal damage along the communication wire route.

Fictional technical diagram of modified earpiece with explosive capability for movie plot
The Timeline Deception and Pre-Attack Planning
The official timeline shows Robinson arriving at 8:29 AM and taking rooftop position at 12:22 PM—just one minute before the fatal shot. FBI Director Kash Patel revealed that Robinson conducted extensive pre-attack planning, including searches for ballistics information and “Charlie Kirk Shot Video” between September 23-24. However, this compressed timeline actually supports the alternative theory, suggesting theatrical positioning rather than careful sniper preparation.
Timeline of events during the Charlie Kirk shooting on September 10, 2025, showing the critical sequence from Robinson’s arrival to his escape
Robinson’s documented searches included Department of Homeland Security facility information and ballistics-related content , providing cover for the sophisticated technical planning required for the alternative method. His confession note left for his roommate and digital evidence trail create a comprehensive false narrative supporting the lone gunman theory.
In the earpiece scenario, Robinson’s rooftop presence becomes performance art creating visual evidence for the false narrative. His 12:24 PM escape provides dramatic conclusion to the staged sniper story while the real assassination team disperses undetected among the chaos.
Investigation Misdirection Strategy and FBI Response
Success depends entirely on misdirecting investigation through orchestrated evidence manipulation, which the extensive FBI investigation has inadvertently validated :
Physical Evidence Planting: Pre-positioned forensic evidence creates an irrefutable paper trail supporting the sniper narrative through Robinson’s DNA on the rifle trigger and strategically placed shell casings. The FBI’s forensic reconstruction of bullet trajectory and identification of the precise shooting location supports this planted evidence.
Witness Testimony Manipulation: Coordinated audio effects ensure multiple witnesses report “hearing a gunshot,” providing testimonial evidence corroborating false physical evidence. The widespread circulation of shooting video footage on social media platforms reinforces the gunshot narrative.
Video Documentation: Security footage showing Robinson’s arrival, positioning, and escape creates complete visual narrative appearing to document the crime comprehensively. The FBI’s analysis of this video evidence as proof of traditional assassination methodology validates the deception.
Communication Evidence: Robinson’s text message confession and Discord communications provide digital proof supporting the lone gunman narrative. The FBI’s investigation into his pre-attack web searches and planning documents reinforces the traditional assassination theory while obscuring alternative explanations.
Exploiting Investigative Vulnerabilities and Security Gaps
This theoretical method exploits several weaknesses in standard protocols that the ongoing investigation has revealed :
Expectation Bias: Investigators expecting traditional assassination find exactly the evidence supporting that assumption, never questioning alternative explanations for observed evidence. The FBI’s comprehensive reconstruction of Robinson’s actions and motivations validates this expectation while potentially overlooking explosive residue or device fragment analysis.
Technology Gap: Standard forensic procedures may not screen for exotic explosive compounds or miniaturized detonation devices integrated with security communications equipment, particularly when ballistic evidence appears conclusive. The absence of detailed autopsy findings prevents discovery of alternative wound patterns.
Timeline Compression: Rapid event sequences prevent detailed real-time analysis that might detect narrative inconsistencies. The FBI’s focus on Robinson’s movements and escape route validates the compressed timeline without questioning the feasibility of accurate long-range shooting with minimal preparation.
Evidence Contamination: Chaotic public assassination aftermath creates evidence manipulation opportunities difficult to detect retroactively. The immediate focus on manhunt operations and social media video analysis diverts attention from alternative forensic examination.
Security Equipment Vulnerabilities and Communication System Risks
Kirk’s use of professional security communications equipment, while providing protection coordination capabilities, created potential vulnerabilities that sophisticated adversaries could exploit :
Equipment Standardization: High-profile individuals typically use standardized security communication systems , creating predictable equipment configurations that technical surveillance could identify and potentially compromise during supply chain or maintenance processes.
Wire Routing Predictability: Professional surveillance earpiece systems follow established routing patterns for operational effectiveness , creating consistent placement opportunities for theoretical device integration along known wire paths.
Security Protocol Gaps: Focus on external threats may not adequately address supply chain compromise of security equipment itself, particularly sophisticated modifications invisible to standard screening procedures.
Implications and Conclusions

The Māori Green Lantern Fighting Misinformation And Disinformation From The Far Right
If technically feasible, this method represents a paradigm shift in assassination methodology, combining targeted killing precision with false flag misdirection capabilities. The earpiece conspiracy demonstrates how sophisticated technology, combined with operational planning, could potentially overcome traditional security measures and investigative protocols.
Parallels to Lebanese pager attacks suggest the technological foundation already exists. Demonstrated ability to weaponize everyday electronics through supply chain infiltration indicates targeting individual communication equipment is not merely theoretical but technically achievable with sufficient resources and expertise.
The FBI’s ongoing investigation, while thorough in examining traditional assassination methodology, may inadvertently validate the deception by confirming the planted evidence trail while not exploring alternative technical explanations for the observed evidence. Director Kash Patel’s acknowledgment that “no theory was dismissed and no stone was left unturned” suggests comprehensive investigation, yet the focus remains on Robinson’s actions and motivations rather than technical forensic analysis of alternative weapon systems.
However, this analysis remains purely speculative—an intellectual exercise in alternative scenario development. The official investigation has established Robinson’s guilt through multiple evidence lines, and this framework should be understood as fictional exploration rather than factual challenge.
The value lies not in undermining legitimate investigations, but highlighting potential vulnerabilities in security protocols and forensic procedures that future protective measures might address. As technology advances, the boundary between science fiction and operational capability continues blurring, making such theoretical exercises increasingly relevant to understanding emerging security challenges.
This earpiece theory presents a sophisticated blend of established technological capabilities , operational complexity , and investigative misdirection illustrating evolving security threats in our digital age. While purely theoretical regarding the Kirk assassination, it demonstrates how unconventional methods might exploit gaps in traditional security assumptions, serving as a valuable reminder that effective protection requires constant adaptation to emerging technological possibilities.
The integration of explosive devices with standard security communications equipment represents a convergence of established technological capabilities with sophisticated operational planning that could theoretically overcome conventional protective measures. Understanding these possibilities, while maintaining respect for ongoing investigations and judicial processes, contributes to enhanced security awareness and protective protocol development for high-profile individuals in an increasingly complex threat environment.
Ngā mihi,
Ivor Jones The Māori Green Lantern
- https://www.1news.co.nz/2025/09/17/charlie-kirk-murder-accused-left-note-under-keyboard/
- https://en.wikipedia.org/wiki/Assassination_of_Charlie_Kirk
- https://abcnews.go.com/US/visual-timeline-charlie-kirk-shooting-unfolded/story?id=125478526
- https://www.axios.com/2024/09/18/hezbollah-pager-explosions-israel-suspicions
- https://www.cnn.com/2024/09/17/middleeast/lebanon-pager-attack-explosions-hezbollah-explainer-intl-latam
- https://en.wikipedia.org/wiki/2024_Lebanon_electronic_device_attacks
- https://www.hollywoodreporter.com/business/business-news/charlie-kirk-assassination-threat-expert-public-event-risk-1236368844/
- https://www.wvbandcoms.com/blogs/blog/how-to-wear-a-radio-earpiece
- https://www.yourvalley.net/stories/as-charlie-kirk-crisscrossed-the-country-security-levels-varied-from-venue-to-venue,615745
- https://crateclub.com/blogs/loadout/how-to-wear-a-two-way-radio-earpiece-a-comprehensive-guide
- https://www.foxnews.com/us/charlie-kirk-assassination-leaves-unanswered-questions-investigators-piece-together-gaps-case
- https://www.reuters.com/graphics/ISRAEL-PALESTINIANS/HEZBOLLAH-PAGERS/mopawkkwjpa/
- https://www.aljazeera.com/features/2025/9/17/lebanons-terrible-year-from-exploding-pagers-to-israeli-occupation
- https://www.aa.com.tr/en/americas/fbi-says-suspect-in-charlie-kirk-killing-conducted-pre-attack-searches/3699243
- https://www.pbs.org/newshour/nation/graphic-video-of-kirk-shooting-was-everywhere-online-showing-how-medias-role-has-changed
- https://www.npr.org/2025/09/18/nx-s1-5542231/kirk-shooting-violence-social-media
- https://www.pbs.org/newshour/nation/as-officials-searched-for-charlie-kirks-shooter-suspect-confessed-to-his-partner-prosecutor-says
- https://www.bbc.com/news/videos/cly0d2dk2gpo
- https://www.nytimes.com/2025/09/10/technology/charlie-kirk-shooting-videos-social-media.html
- https://www.unilad.com/news/us-news/charlie-kirk-security-trump-secret-service-agent-019893-20250912
- https://www.yahoo.com/news/articles/fact-check-no-evidence-secret-112234684.html
- https://abcnews.go.com/US/charlie-kirk-shooting-fbi-appeals-tips-manhunt-continues/story?id=125469211
- https://www.reuters.com/world/us/trump-campaign-turns-secure-hardware-after-hacking-incident-2024-10-11/
- https://www.electrospaces.net/2025/03/the-equipment-that-trumps-national.html
- https://www.reddit.com/r/explainlikeimfive/comments/87w9ib/eli5_is_there_a_wire_going_through_the_clear/
- https://www.fec.gov/help-candidates-and-committees/making-disbursements/candidate-and-officeholder-security/
- https://www.goodmorningamerica.com/news/story/dept-homeland-security-enhances-security-charlie-kirks-funeral-125712750
- https://www.secretservice.gov/about/faq/general
- https://www.cnn.com/2025/04/09/politics/election-security-systems-trump-invs
- https://www.instructables.com/Secret-Agent-Earphones/
- https://www.cisa.gov/topics/election-security