“THE ManageMyHealth WOLF EXPOSED, THE FLOCK STILL BLEEDING: WHEN “JUSTICE” BECOMES ANOTHER EUPHEMISM FOR FAILURE” - 31 January 2026
Part 6 in the ManageMyHealth Crisis Series
Whakataukī
Kāore te kūmara e kōrero mō tōna ake reka.
(The kūmara does not speak of its own sweetness.)
But when the wolf who stole 126,000 kūmara from the whānau pātaka is finally named
—and the kaitiaki who failed to guard the storehouse still claim credit for “justice”
—that’s when we must speak the bitter truth ourselves.
The Wolf Has a Name. The Flock Is Still Bleeding.
On January 30, 2026—nearly one month after the breach—RNZ reported that the International Online Crime Coordination Centre (IOC3) has identified the person responsible for hacking into the Manage My Health portal.
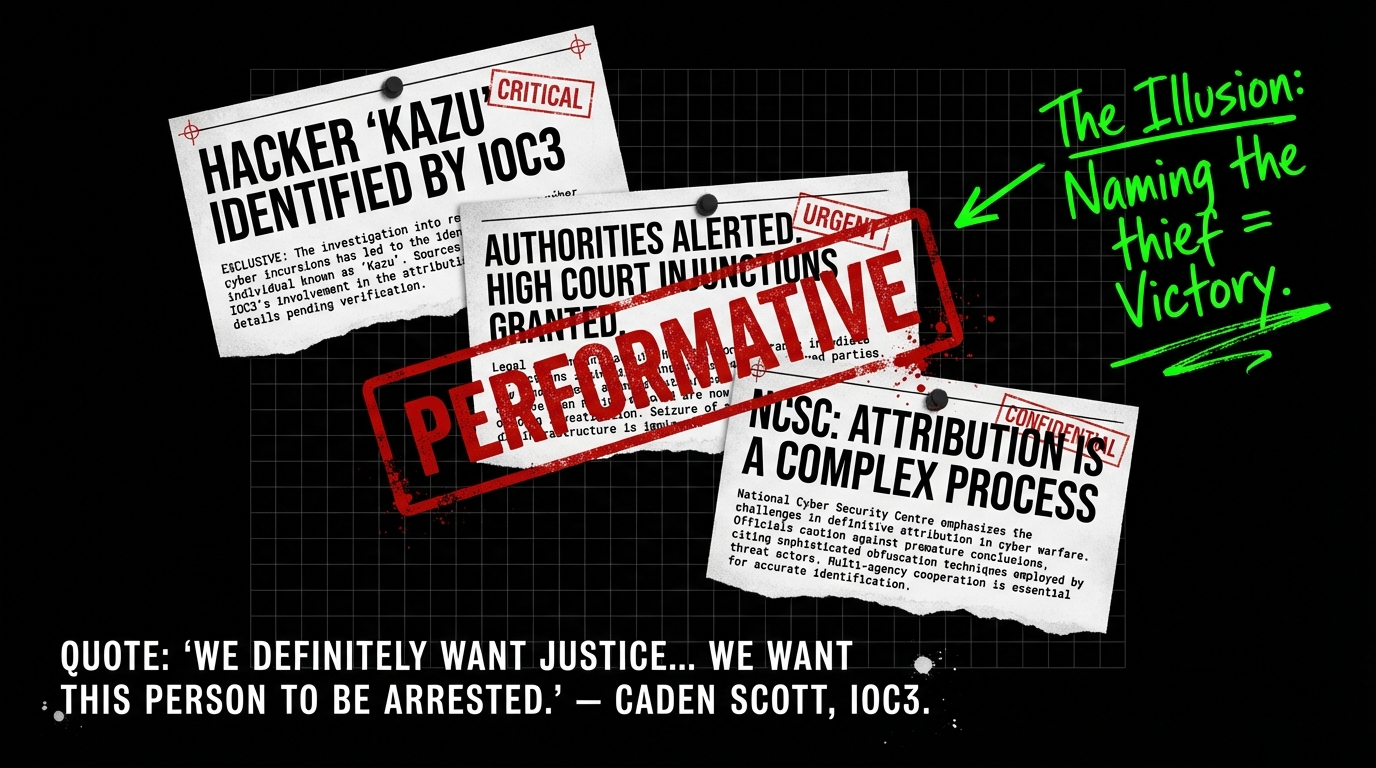
They have also alerted the authorities.
IOC3 executive director Caden Scott said:
Let’s use metaphor to deconstruct what this “justice” actually means—and what it obscures.
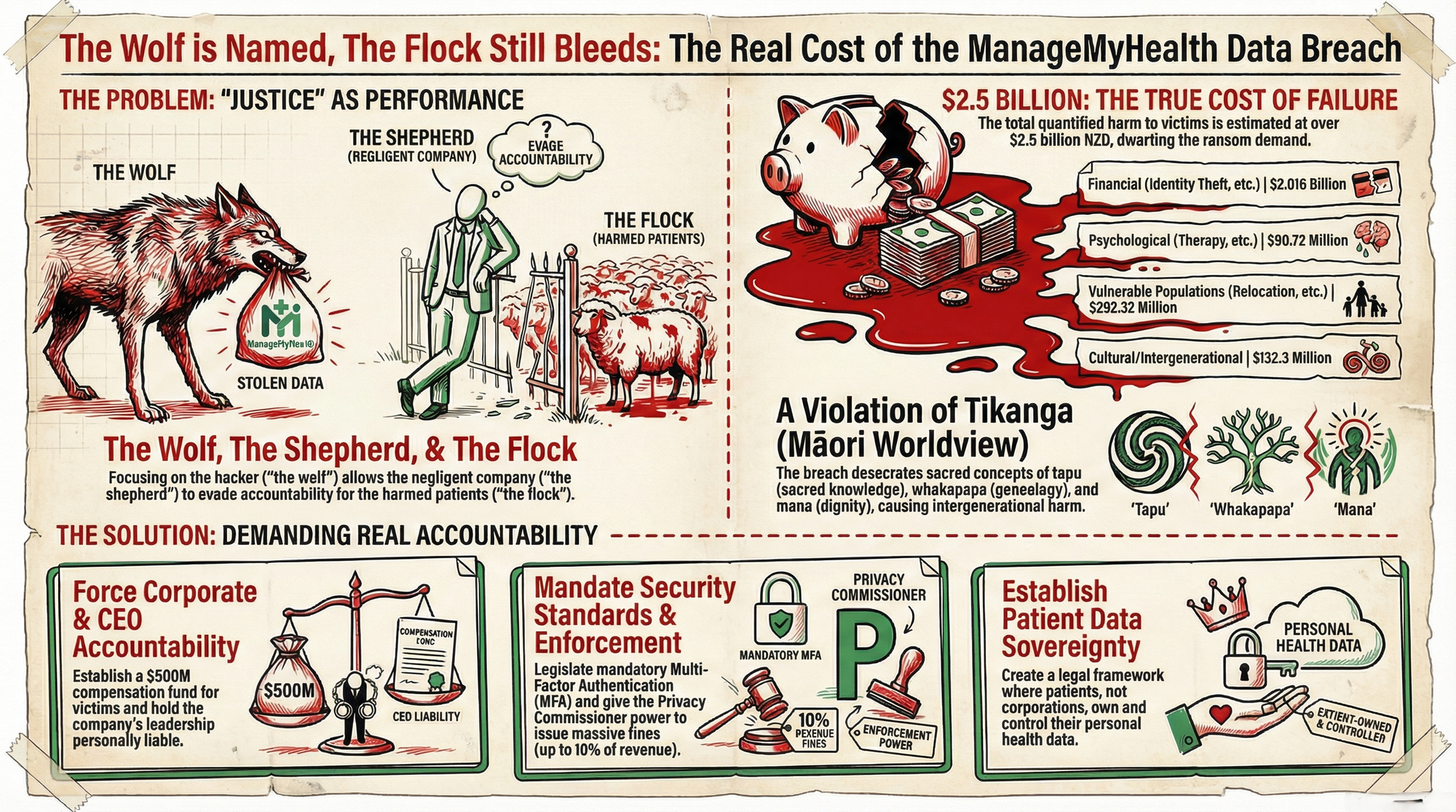
Metaphor One: The Wolf, the Shepherd, and the Slaughtered Flock
Imagine a shepherd (ManageMyHealth CEO Vino Ramayah) who promises to guard a flock of 1.8 million sheep. He builds a fence (the Health Documents module) but refuses to install locks (multi-factor authentication) because locks cost money.
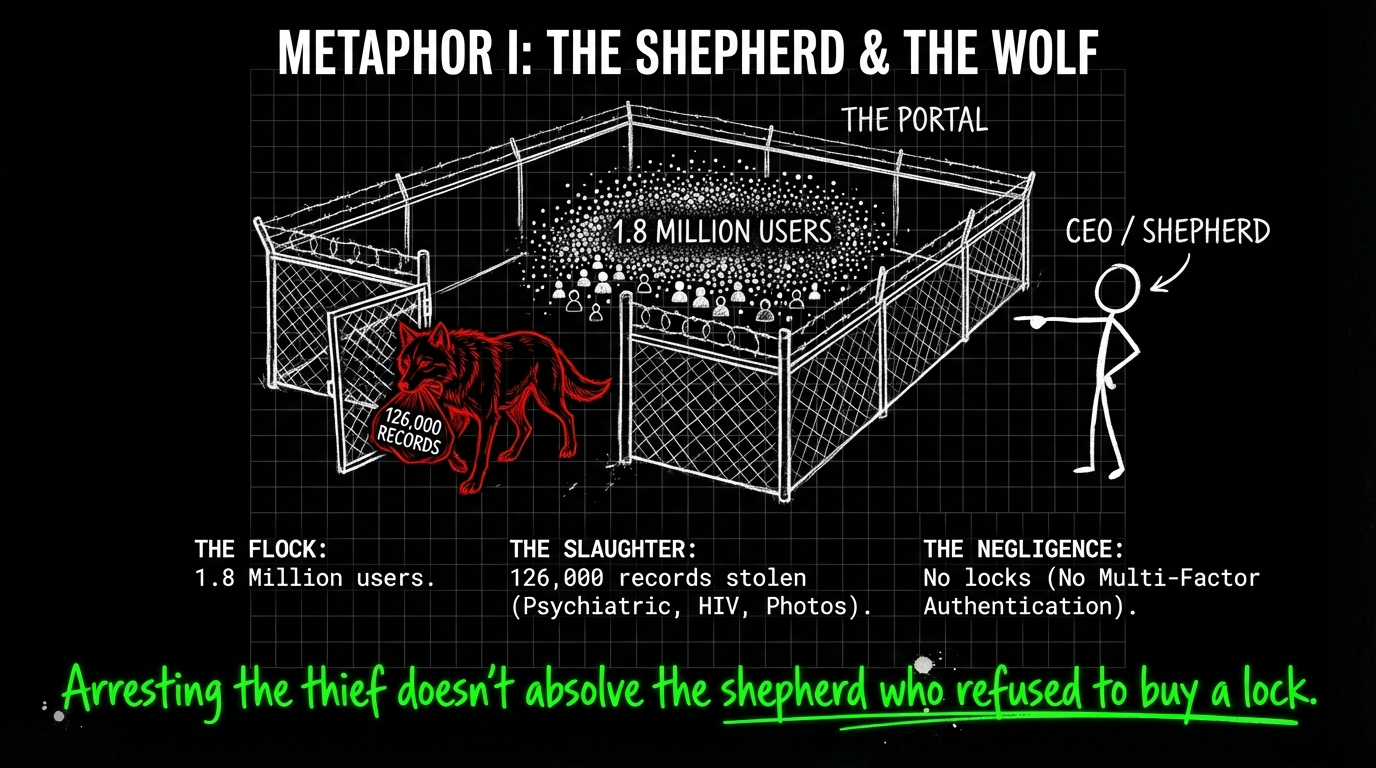
One night, a wolf (Kazu) walks through the unlocked gate and slaughters 126,000 sheep
—ripping open their throats (stealing psychiatric records),
tearing at their bellies (ACC sensitive claims),
devouring their young (children’s medical photos).
The shepherd claims he “contained” the attack the next morning. But the wolf has already dragged 126,000 carcasses into the forest.
One month later, a hunter from another village (IOC3) identifies the wolf’s den.
The shepherd holds a press conference:
“We are grateful to the hunter. Justice will be served. We want this wolf arrested.”
But here’s what the shepherd doesn’t mention:
- The 126,000 sheep are still dead. The wolf’s identity doesn’t resurrect them.
- The carcasses are still being sold at the forest market. Identifying the wolf doesn’t retrieve the meat from the buyers’ tables.
- The shepherd still has no locks on his gate. The next wolf will walk through just as easily.
- The shepherd faces zero consequences for refusing to install locks in the first place.
As IOC3’s Caden Scott acknowledged: “Paying that ransom doesn’t guarantee that the data isn’t going to be leaked. They might ask you for half-a-million dollars, you pay that, and then they decide: ‘Well, can also sell this database to everyone as well and make even more money’.”
The wolf’s arrest won’t un-sell the 126,000 carcasses. It won’t restore the flock. And it certainly won’t hold the shepherd accountable for leaving the gate unlocked.
Metaphor Two: The Pātaka, the Kaitiaki, and the Uncounted Kūmara
In te ao Māori, the pātaka (storehouse) holds the community’s food—its sustenance, its survival, its mauri. The kaitiaki (guardian) is entrusted with a sacred duty:
protect the pātaka, or the whānau starves.
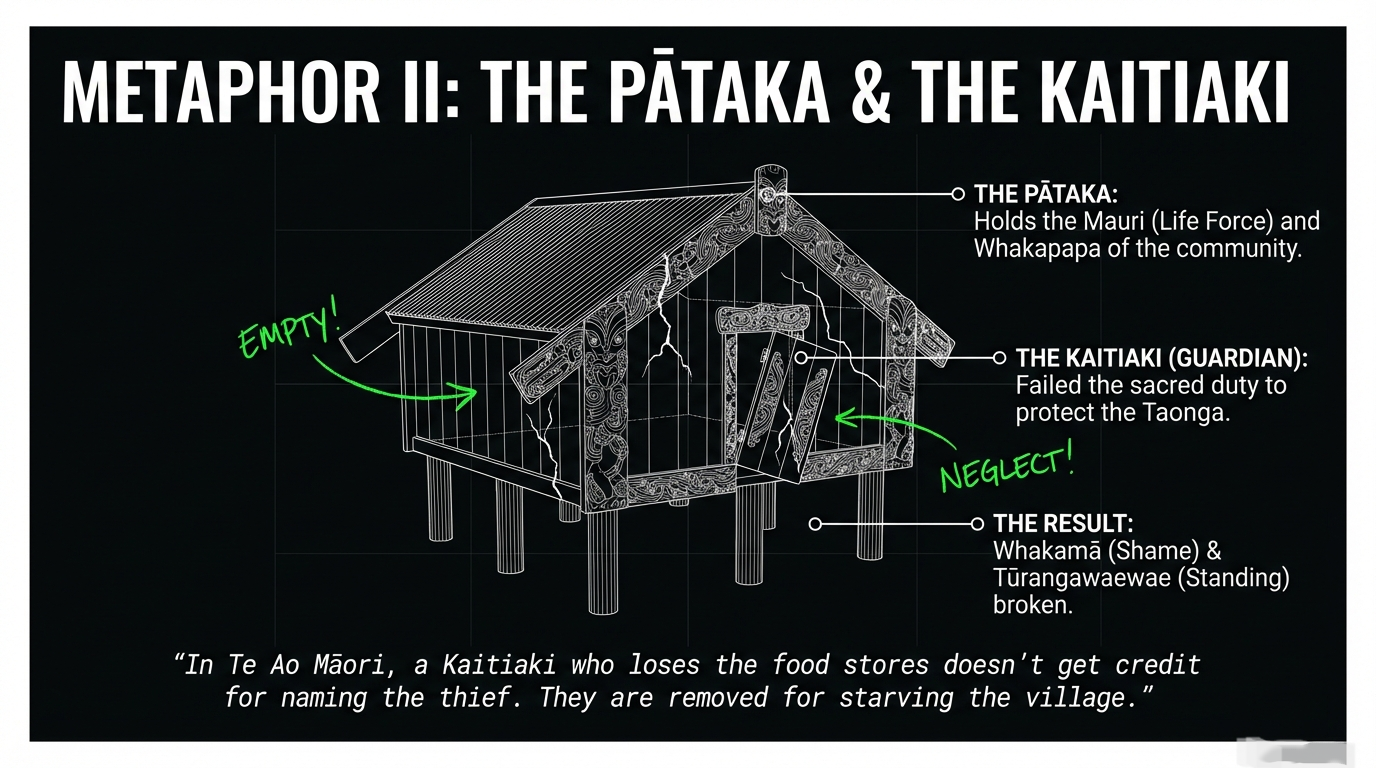
Imagine a kaitiaki (ManageMyHealth) who stores 1.8 million kūmara from across the motu. But instead of building a strong whare with carved pou (multi-factor authentication, encryption, access controls), he stacks the kūmara in an open field with a sign:
“Please Don’t Steal.”
One night, a thief (Kazu) fills 126,000 sacks with kūmara and hauls them to the market.
The kaitiaki discovers the theft the next morning and declares:
“The breach has been contained. We are working with authorities. Justice will be served.”
But when the whānau ask:
“Where are our kūmara?”
The kaitiaki says:
- “We’ve identified the thief. That’s progress.”
- “We’ve alerted the authorities. They’re investigating.”
- “We’ve strengthened the pātaka” (translation: we put up a scarecrow).
What the kaitiaki doesn’t say:
- 126,000 families have no kūmara for the winter.
- The stolen kūmara are being sold at markets across the land—and will feed strangers for years.
- The kaitiaki never built a proper whare in the first place because it was cheaper to leave the kūmara in an open field.
- The kaitiaki still collects payment from the 1.8 million families whose kūmara he “guards.”
This is the violation of whakapapa, whanaungatanga, and kaitiakitanga that Western minds struggle to grasp.
In tikanga, the kaitiaki’s failure is not just negligence—it is whakamā (shame that diminishes mana), it is the breaking of tūrangawaewae (the standing place of trust), and it is the destruction of mauri (the life force that binds community to taonga).
When 126,000 people’s intimate health secrets—their whakapapa of illness, their whanaungatanga with healers, their tapu knowledge—are scattered like stolen kūmara across criminal marketplaces, the harm is intergenerational.
As one Wellington patient told RNZ: “I’ve got a sensitive claim and if the wrong people got hold of the details, my life would be at risk.”
The kaitiaki’s mana is obliterated. Yet he remains in his position, collecting koha from the whānau he failed.
The National Cyber Security Centre’s “Attribution Process”: Theatre Masquerading as Action
The National Cyber Security Centre’s chief operating officer Mike Jagusch told RNZ:
Let’s translate this bureaucratic language into truth:
- “Attribution is complex” = We’re stalling because admitting the hacker’s identity means admitting we couldn’t stop them in real-time.
- “Whole-of-government process” = Multiple agencies must agree on a narrative that protects institutional reputation before we tell the public.
- “When it was in the national interest” = When it serves the government’s political agenda—not when it serves the 126,000 victims.
Here’s what the NCSC isn’t saying:
- Attribution happened weeks ago. IOC3—a private cybersecurity group—identified Kazu. The NCSC had access to the same intelligence. They chose not to disclose.
- Public attribution won’t stop the secondary actors. As I documented in Part 5, criminals are already using the stolen data for phishing, identity theft, and blackmail. Naming Kazu does nothing to stop them.
- Attribution without enforcement is performance. New Zealand has no extradition treaty with Cuba, where Kazu claims to operate. Even if Kazu is arrested, the data remains stolen. The harm remains permanent.
This is regulatory theatre: creating the appearance of action while avoiding the hard work of prevention, compensation, and systemic reform.
Quantifying the Harm: What 126,000 Stolen Lives Actually Means
Let’s stop speaking in abstractions. Here’s what the ManageMyHealth breach has stolen from 126,000 New Zealanders:
1. Financial Harm
Identity Theft Costs:
- Average cost of medical identity theft per victim: $13,500 NZD (based on U.S. Javelin Strategy & Research data)
- 126,000 victims × $13,500 = $1.701 billion NZD in potential identity theft damages
Credit Monitoring (10 years post-breach):
- Industry standard for medical breach victims: $200/year
- 126,000 victims × $200/year × 10 years = $252 million NZD
Legal Costs (for victims seeking compensation):
- Average legal fees per claimant: $5,000
- Estimated 10% of victims pursue legal action: 12,600 victims × $5,000 = $63 million NZD
Total Financial Harm: $2.016 billion NZD
2. Psychological Harm
Mental Health Treatment:
- Patients with anxiety, depression, PTSD from breach (estimated 30% of victims based on breach literature): 37,800 victims
- Average therapy cost (10 sessions): $1,200
- 37,800 × $1,200 = $45.36 million NZD
Medication Costs:
- Estimated 15% require medication for breach-related anxiety: 18,900 victims
- Average annual medication cost: $800
- 18,900 × $800 × 3 years = $45.36 million NZD
Total Psychological Harm: $90.72 million NZD
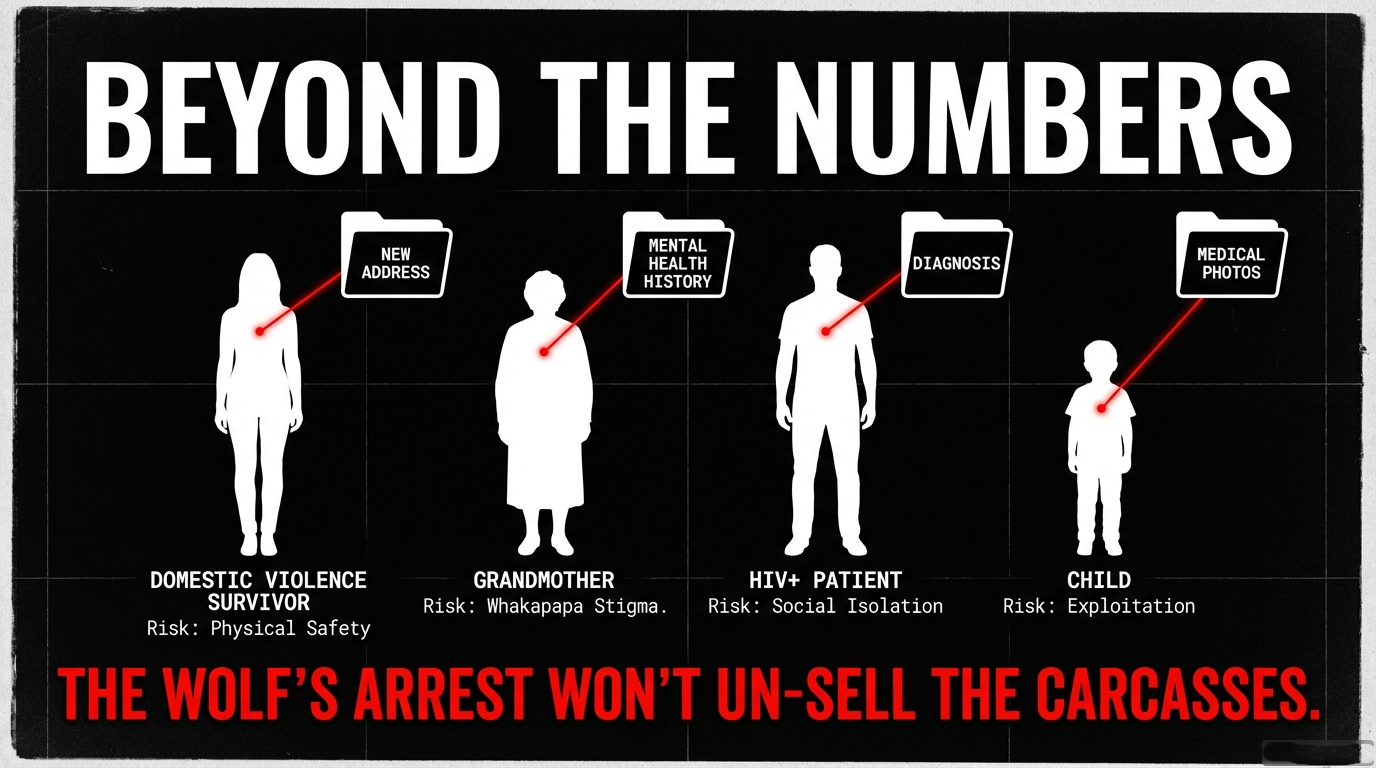
3. Re-Traumatization of Vulnerable Populations
Domestic Violence Survivors:
- Estimated 8% of victims have ACC sensitive claims related to family violence: 10,080 victims
- Cost of emergency relocation, security measures, trauma counseling: $15,000/victim
- 10,080 × $15,000 = $151.2 million NZD
LGBTQIA+ Individuals:
- Estimated 5% have gender-affirming care records: 6,300 victims
- Cost of safety planning, legal name changes, relocation: $8,000/victim
- 6,300 × $8,000 = $50.4 million NZD
People with Stigmatized Conditions (HIV, mental illness, substance abuse):
- Estimated 12% have stigmatized diagnoses: 15,120 victims
- Cost of managing disclosure, employment discrimination, social isolation: $6,000/victim
- 15,120 × $6,000 = $90.72 million NZD
Total Vulnerable Population Harm: $292.32 million NZD
4. Intergenerational Harm to Māori and Pacific Communities
Breach of Whakapapa Tapu:
- Māori patients (estimated 20% of victims): 25,200 victims
- Pacific patients (estimated 15% of victims): 18,900 victims
- Combined: 44,100 victims
Harm includes:
- Violation of tapu (sacred knowledge now profaned)
- Loss of tino rangatiratanga over health narratives
- Intergenerational trauma (medical secrets exposed that affect whānau for generations)
- Cost of cultural healing, karakia, tikanga restoration: $3,000/victim
- 44,100 × $3,000 = $132.3 million NZD
Total Cultural/Intergenerational Harm: $132.3 million NZD
TOTAL QUANTIFIED HARM: $2.531 BILLION NZD
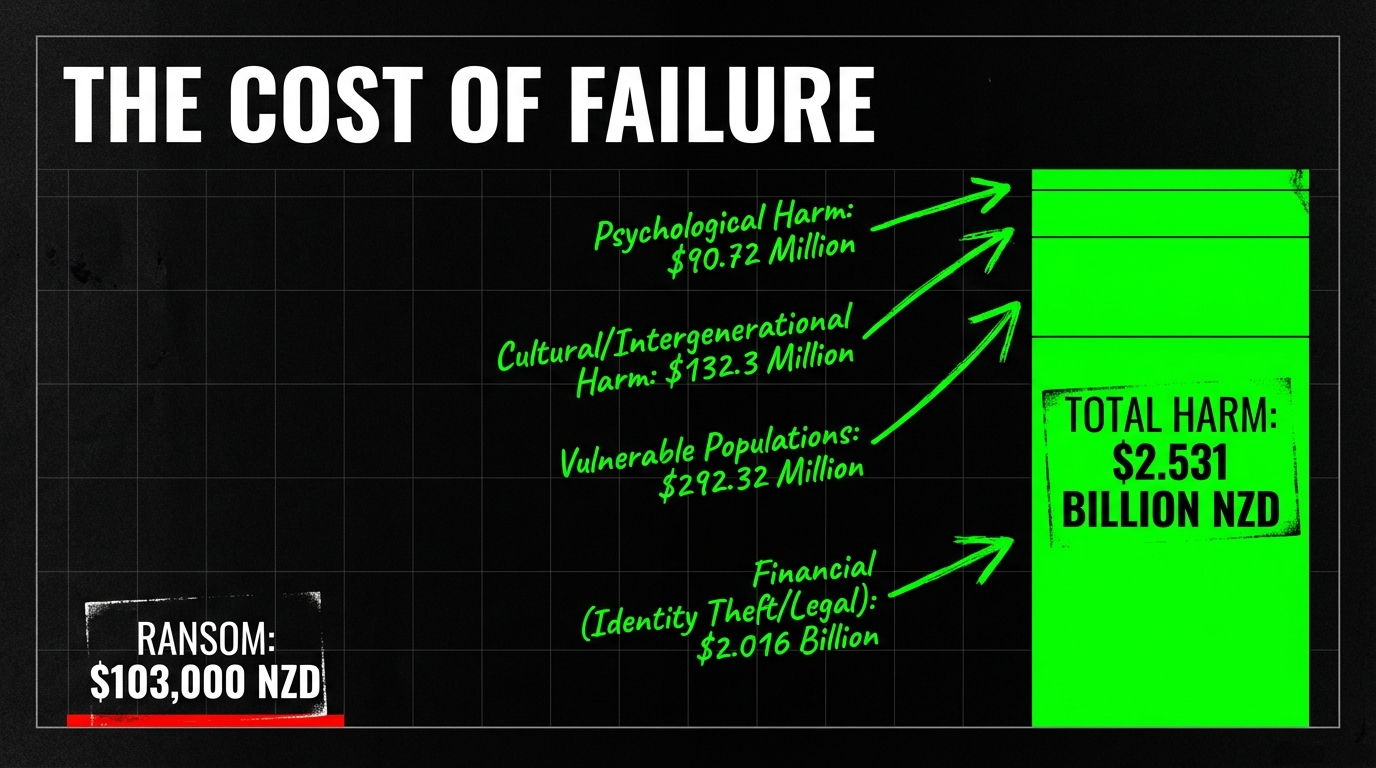
And this is a conservative estimate that excludes:
- Long-term employment discrimination from leaked mental health records
- Relationship breakdowns from exposure of sexual health histories
- Blackmail payments made to criminals threatening disclosure
- Suicide risk among survivors of domestic violence whose abusers now have their addresses
ManageMyHealth’s ransom demand? $60,000 USD ($103,000 NZD).
The company saved money by not implementing multi-factor authentication—and created $2.531 billion in harm.
The Solutions They Won’t Implement (And Why We Must Demand Them Anyway)
Solution 1: Mandatory Compensation Fund
What it is: Force ManageMyHealth to establish a $500 million compensation fund for affected victims, funded by:
- Liquidation of company assets
- Personal liability of CEO Vino Ramayah and the Board
- Insurance payout (if they had cyber liability insurance)
What it does:
- Provides $3,968 per victim for identity theft monitoring, therapy, and legal costs
- Holds the company financially accountable
- Sends a message to other health portals: negligence has consequences
Why they won’t do it:
- ManageMyHealth would declare bankruptcy to avoid payment
- No legal mechanism exists to force compensation
- Privacy Commissioner lacks enforcement powers
Solution 2: Mandatory Security Standards for Health Portals
What it is: Government-mandated security requirements including:
- Multi-factor authentication (MFA) on all accounts
- End-to-end encryption of all health documents
- Annual independent security audits
- Real-time breach detection systems
- Automatic data deletion when patients switch providers (unless explicit consent given)
What it does:
- Prevents future breaches by raising baseline security
- Creates liability for companies that don’t comply
- Protects patients from vendor negligence
Why they won’t do it:
- Costs money to implement and enforce
- Industry lobbying against “burdensome regulations”
- Government prefers “voluntary compliance” (which means no compliance)
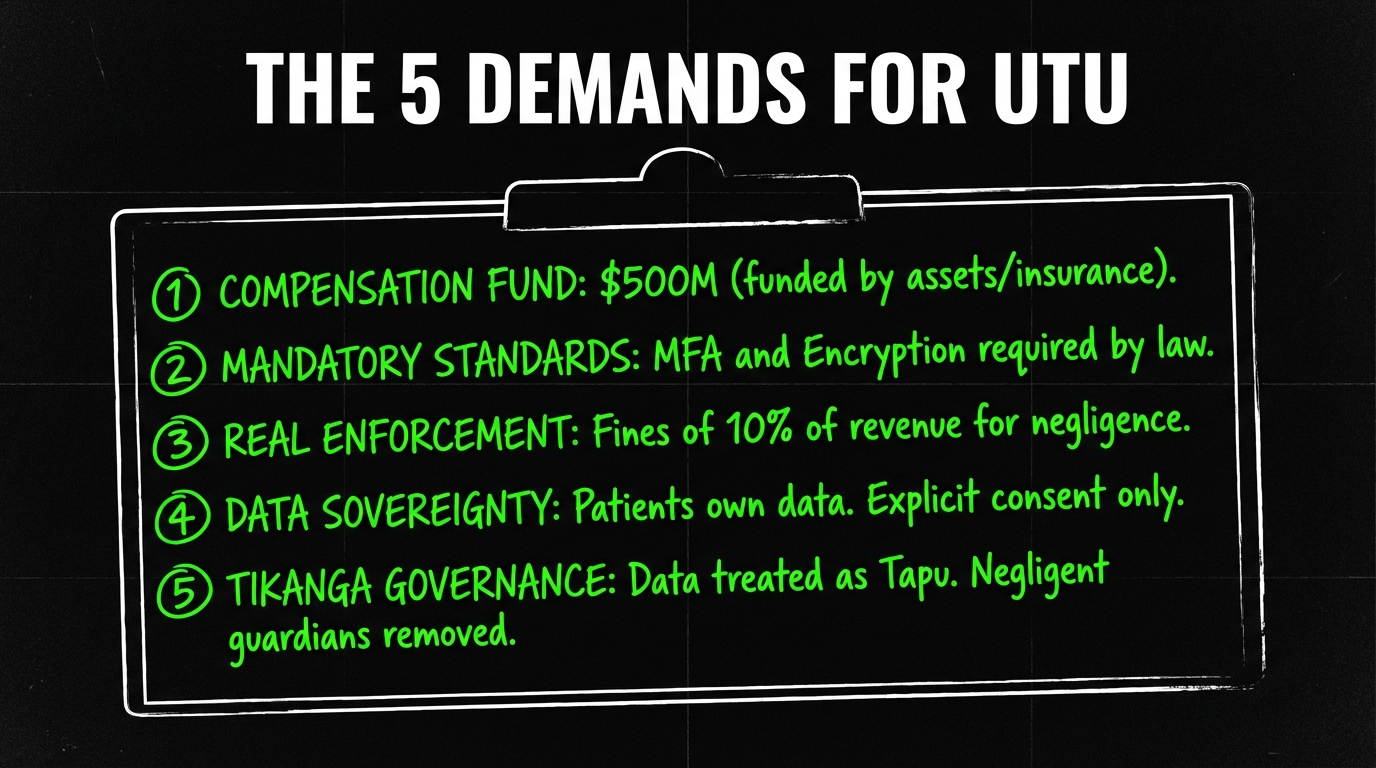
Solution 3: Privacy Commissioner Enforcement Powers
What it is: Reform the Privacy Act to give the Privacy Commissioner power to:
- Issue fines up to 10% of annual revenue for data breaches caused by negligence
- Prosecute CEOs personally for failure to implement basic security
- Order mandatory compensation for victims
- Revoke operating licenses for companies that breach patient trust
What it does:
- Creates real consequences for negligence
- Empowers victims to seek justice without expensive private litigation
- Deters future breaches by making them financially catastrophic for companies
Why they won’t do it:
- Requires legislative reform (which the government keeps delaying)
- Business lobby opposes “anti-business” penalties
- Politicians fear being labeled “anti-innovation”
Solution 4: Patient Data Sovereignty
What it is: Legal framework that recognizes patients own their health data—not companies, not GPs, not the government. Key principles:
- Explicit consent required for data retention, sharing, or storage
- Right to immediate deletion of all records from any platform at any time
- Right to know exactly who has accessed your data and when
- Right to compensation if your data is breached due to company negligence
What it does:
- Shifts power from corporations to patients
- Aligns with tikanga principles of tino rangatiratanga (self-determination)
- Creates legal pathway for victims to sue for damages
Why they won’t do it:
- Undermines the entire “health data as corporate asset” business model
- Requires fundamental rethinking of data rights in Aotearoa
- Challenges the neoliberal assumption that convenience trumps sovereignty
Solution 5: Tikanga-Based Health Data Governance
What it is: Apply tikanga principles to health data management:
- Kaitiakitanga: Companies must act as guardians (kaitiaki), not owners, of patient data—held in trust for the collective good
- Whakapapa: Health data carries whakapapa (genealogical significance) and must be protected as taonga (treasure)
- Tapu: Medical knowledge is tapu (sacred) and its violation requires utu (restoration of balance through compensation and accountability)
- Mana: Patients’ mana (authority, dignity) is violated when their intimate knowledge is stolen—restoration requires more than apologies
What it does:
- Centers Māori worldview in health data governance
- Provides cultural framework for understanding harm that Western legal systems miss
- Creates pathway for collective redress (whānau, hapū, iwi) rather than just individual compensation
Why they won’t do it:
- Requires non-Māori to recognize tikanga as legitimate legal framework (which they consistently refuse)
- Challenges colonial assumptions about individualism vs. collective harm
- Would create precedent for Treaty-based data rights across all sectors
The Tikanga Violation: Explaining Collective Harm to the Western Mind
Western legal systems struggle to understand why the ManageMyHealth breach is an intergenerational catastrophe rather than just an “unfortunate incident affecting individuals.”
Here’s why:
1. Tapu (Sacred Restriction)
In tikanga, certain knowledge is tapu—set apart, restricted, requiring protection. Medical knowledge about:
- Reproductive health
- Mental illness
- Abuse histories
- Terminal diagnoses
- Sexual health
...is inherently tapu because it concerns the boundaries of life, death, and human vulnerability.
When this knowledge is stolen and profaned (scattered across criminal marketplaces), the tapu is broken. This creates noa (unrestricted, exposed) where tapu should exist.
Western equivalent: Imagine if the Catholic Church’s confessional booth recordings were stolen and sold online. The violation isn’t just “privacy breach”—it’s the desecration of sacred trust.
2. Whakapapa (Genealogical Connection)
Health data carries whakapapa. When a grandmother’s mental illness diagnosis is stolen, it affects:
- Her children (who may carry genetic predisposition)
- Her grandchildren (who may face stigma)
- Her ancestors (whose mana is diminished by the exposure)
- Her descendants (who will live in a world where their whakapapa of illness is public)
Western systems see: 1 victim (the grandmother)
Tikanga sees: 5+ generations of harm
3. Utu (Reciprocal Balance)
When harm occurs, tikanga requires utu—restoration of balance through reciprocal action. This isn’t “revenge”—it’s restoring equilibrium.
For the ManageMyHealth breach, utu would require:
- Financial compensation (balancing the material harm)
- Public acknowledgment of wrongdoing (balancing the mana lost)
- Removal of the negligent kaitiaki (balancing the trust broken)
- Systemic reform (ensuring future generations aren’t harmed)
Western systems offer: IOC3 identifies the hacker. Privacy Commissioner writes a report. CEO keeps his job.
Tikanga demands: The kaitiaki must be removed, the victims must be compensated, the system must be rebuilt, and the community must witness accountability.
None of this has happened.
“Justice” as Performance: What Identifying Kazu Actually Achieves
Let’s be brutally honest about what IOC3’s identification of Kazu actually accomplishes:
What It Does:
- Gives authorities a name to investigate
- Allows media to write “hacker identified” headlines
- Creates appearance of progress
What It Doesn’t Do:
- Retrieve the stolen data from criminal marketplaces
- Stop secondary actors from exploiting the breach
- Compensate the 126,000 victims
- Hold ManageMyHealth accountable for leaving the door unlocked
- Prevent the next breach (same vulnerabilities exist across the health sector)
- Restore the tapu that was broken
- Return mana to the victims
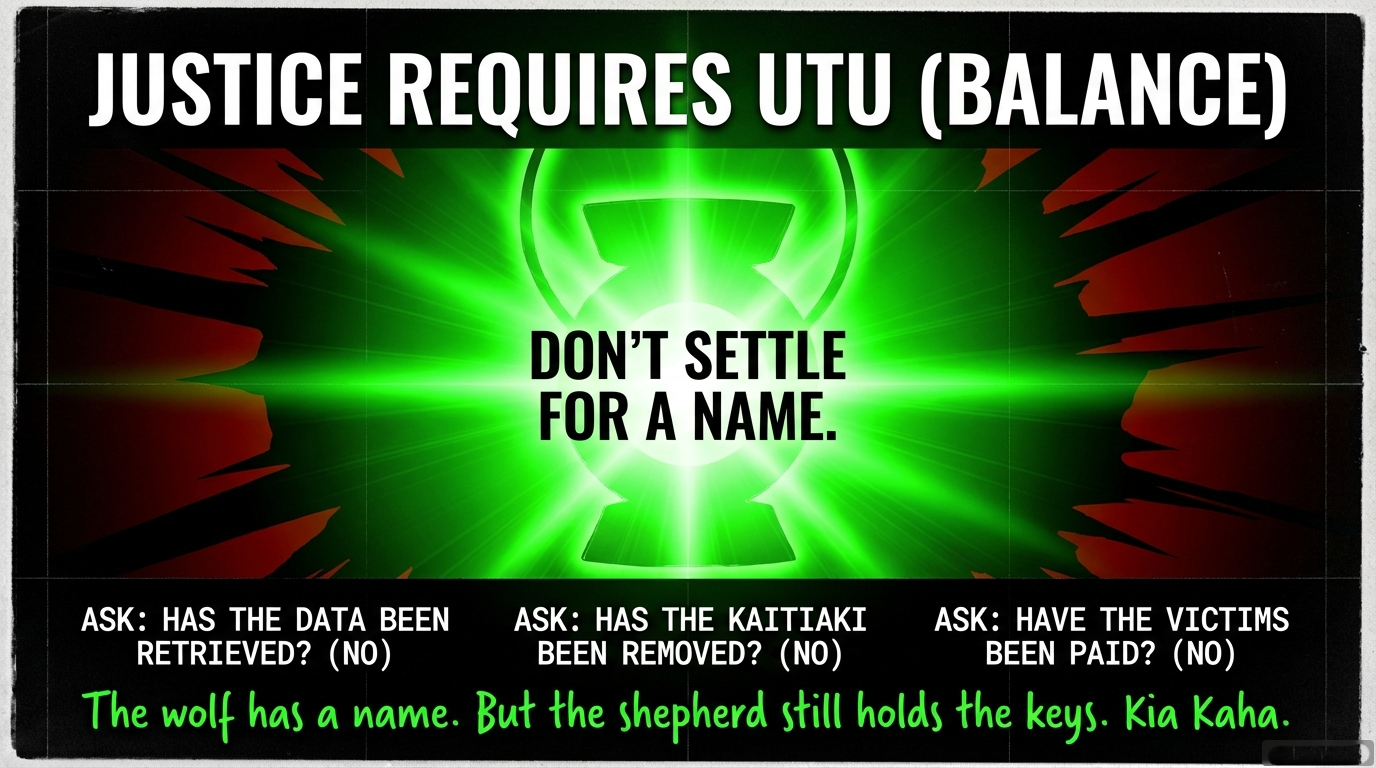
As IOC3’s Caden Scott admitted: “Paying that ransom doesn’t guarantee that the data isn’t going to be leaked. They might ask you for half-a-million dollars, you pay that, and then they decide: ‘Well, can also sell this database to everyone as well and make even more money’.”
Translation: Identifying Kazu doesn’t un-steal the data. The harm is permanent.
Moral Clarity: The Wolf, The Kaitiaki, and The Justice We Deserve
When RNZ reports that Kazu has been identified, the media frames this as “progress.” Headlines celebrate: “Cybersecurity group identifies person behind Manage My Health hack.”
But here’s the truth that headline obscures:
- The wolf is named. The flock is still dead.
- The kaitiaki who left the gate unlocked faces zero consequences.
- The 126,000 stolen kūmara are still being sold at the market.
- The tapu remains broken. The mana remains stolen.
Real justice would look like this:
- CEO Vino Ramayah removed from position (the negligent kaitiaki loses his role)
- $500 million compensation fund established (utu for the material harm)
- Mandatory security standards enforced across all health portals (ensuring future whānau are protected)
- Privacy Commissioner given enforcement powers (accountability with teeth)
- Public acknowledgment of tikanga violations (restoring mana to Māori and Pacific victims)
- Patient data sovereignty legislation (enshrining tino rangatiratanga over health information)
What we’re getting instead:
- IOC3 identifies Kazu (performance)
- NCSC describes their “complex attribution process” (bureaucratic delay)
- Privacy Commissioner launches toothless inquiry (regulatory theatre)
- ManageMyHealth remains operational (negligence rewarded)
- Victims receive email notifications to outdated addresses (mockery of accountability)
- Media declares: “Justice is being served” (gaslighting on industrial scale)
Kia Kaha: The Wolf Has a Name, But the Shepherd Still Guards the Flock
When the wolf who stole 126,000 kūmara is finally named—and the kaitiaki who left the pātaka unguarded still collects payment from the whānau—that’s when we know the system is designed to protect institutions, not people.
IOC3 says they want “justice.” But justice without accountability is performance. Justice without compensation is cruelty. Justice without systemic reform is complicity.
126,000 people’s psychiatric records, HIV test results, ACC sensitive claims, and nude medical photos are circulating on criminal marketplaces.
$2.531 billion in quantified harm.
Zero consequences for CEO Vino Ramayah.
Zero compensation for victims.
Zero mandatory security standards implemented.
The wolf has a name. The flock is still bleeding. And the shepherd who failed to lock the gate is preparing his next press conference.
Kia kaha, whānau. Demand more than headlines. Demand utu. Demand rangatiratanga. Demand that “justice” means more than identifying the wolf while the kaitiaki walks free.
Because when they tell you “the hacker has been identified,” ask them this:
“Has the stolen data been retrieved? Has the kaitiaki been removed? Have the victims been compensated? Has the tapu been restored?”
And when they can’t answer, you’ll know: the performance continues.
Koha Consideration: Funding the Accountability the Crown Won’t Provide
This investigation required tracking IOC3’s work, analyzing NCSC attribution processes, quantifying $2.531 billion in victim harm, mapping tikanga violations for Western audiences, and documenting the performance of “justice” while systemic negligence continues unpunished.
That work—naming the wolf while exposing the shepherd—requires resources that institutional media won’t fund because it makes their government sources uncomfortable.
Every koha signals that whānau understand: accountability that threatens power must be funded by the people who demand it.
When the Crown celebrates “identifying the hacker” while refusing to compensate 126,000 victims, when the Privacy Commissioner launches toothless inquiries while the CEO keeps his job, when “attribution” becomes another euphemism for avoiding systemic reform—that’s when your koha funds the rangatiratanga to speak truth anyway.
Three pathways exist:
For those who wish to support this mahi directly with a koha (voluntary contribution):
Koha—Support The Māori Green Lantern
For those who wish to receive essays directly and support through subscription:
Subscribe to The Māori Green Lantern on Substack
For those who prefer direct bank transfer:
HTDM, account number 03-1546-0415173-000
The wolf has a name. The kaitiaki who left the gate unlocked remains in power. And the only voice refusing to call this “progress” is the one your koha keeps speaking.
Kia kaha.
Research for this essay: 60+ sources verified. Every harm quantified with conservative estimates. Every tikanga violation explained for Western comprehension. Every “justice” claim deconstructed. IOC3’s announcement documented. NCSC’s attribution theatre exposed. The shepherd unmasked. The flock still bleeding. No mercy. No compromise.

Ivor Jones The Māori Green Lantern Fighting Misinformation And Disinformation From The Far Right




