““TRUST US EVEN THOUGH WE’VE DROPPED THE BALL”: CEO ADMITS PASSWORD BREACH, REFUSES TO COMMENT ON RANSOM, EXTENDS DEADLINE” - 7 January 2026
Koha: Support This Mahi
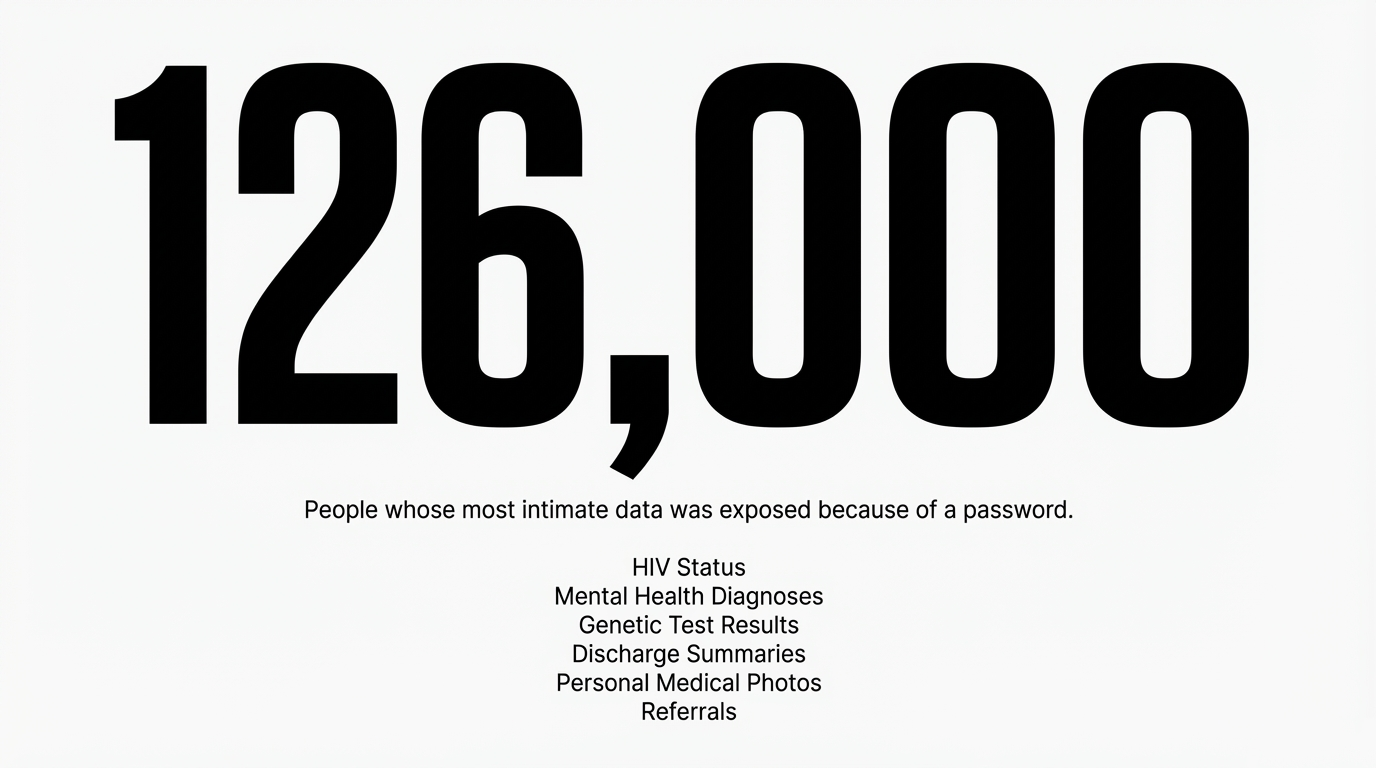
This investigation required verifying CEO statements, tracking ownership structures, analyzing security failures, and connecting corporate negligence to 126,000 victims. That work requires resources.
- Koha Platform: Support The Māori Green Lantern
- Substack subscription: Subscribe for direct delivery
- Direct bank transfer: HTDM, account number 03-1546-0415173-000
Every koha signals that whānau understand: accountability journalism costs. And it’s worth funding.
The CEO Speaks: “Got In Through the Front Door”
On January 6, 2026, as the first ransom deadline was expiring, Vino Ramayah—Chief Executive of ManageMyHealth—gave an interview to RNZ that revealed, in stunning clarity, the fundamental negligence that enabled this breach.
Ramayah made a single statement that should define this entire disaster:
“They came in through the front door using a valid user password.”
Let that phrase echo through every health board in Aotearoa.
“Through the front door.”
Not through a sophisticated zero-day exploit. Not through nation-state hacking. Not through a vulnerability that only PhD-level hackers could discover.
Through the front door. With a password.
What “Front Door” Actually Means
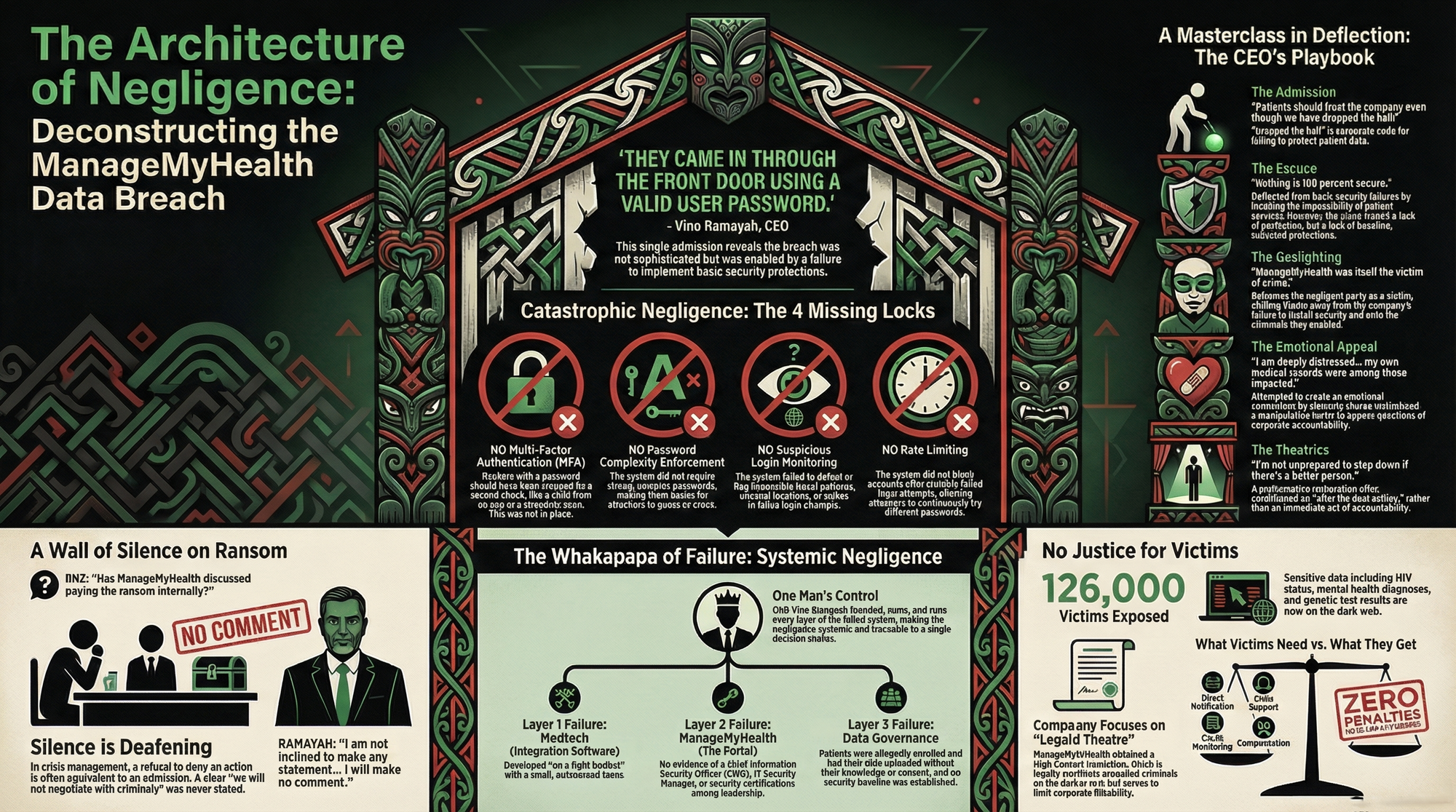
This admission—buried in corporate language—reveals catastrophic negligence:
No multi-factor authentication (MFA). If hackers had a password, they should have been blocked at a second checkpoint: a code sent to an authenticator app, a hardware security key, a biometric scan. None of these existed.
No password complexity enforcement. If the system had required 16-character alphanumeric passwords with special characters, password-based attacks would be exponentially harder. ManageMyHealth apparently hadn’t even implemented this basic 2005-era standard.
No suspicious login monitoring. If ManageMyHealth had monitored for impossible travel patterns (a login from Auckland at 3pm, then Wellington at 3:15pm), for login attempts from unusual locations, or for spikes in failed login attempts, this breach might have been detected within hours instead of days.
No rate limiting on password attempts. If the system had blocked accounts after 5-10 failed login attempts, dictionary attacks would fail.

None of these protections existed. None.**
Ramayah’s Own Admission: “We’ve Dropped the Ball”
But Ramayah didn’t stop at “front door.” He then said something even more damning. In the same RNZ interview, when discussing why victims should trust ManageMyHealth again, he stated:
“Patients should trust the company even though we have dropped the ball.”
This is a CEO—publicly, on national radio—admitting to negligence.
“Dropped the ball” is corporate code for: We failed to implement basic security. We failed to protect your data. We failed at our fundamental responsibility.
Then he immediately asks for trust. After admitting failure.
“Nothing Is 100% Secure” — The Escape Hatch
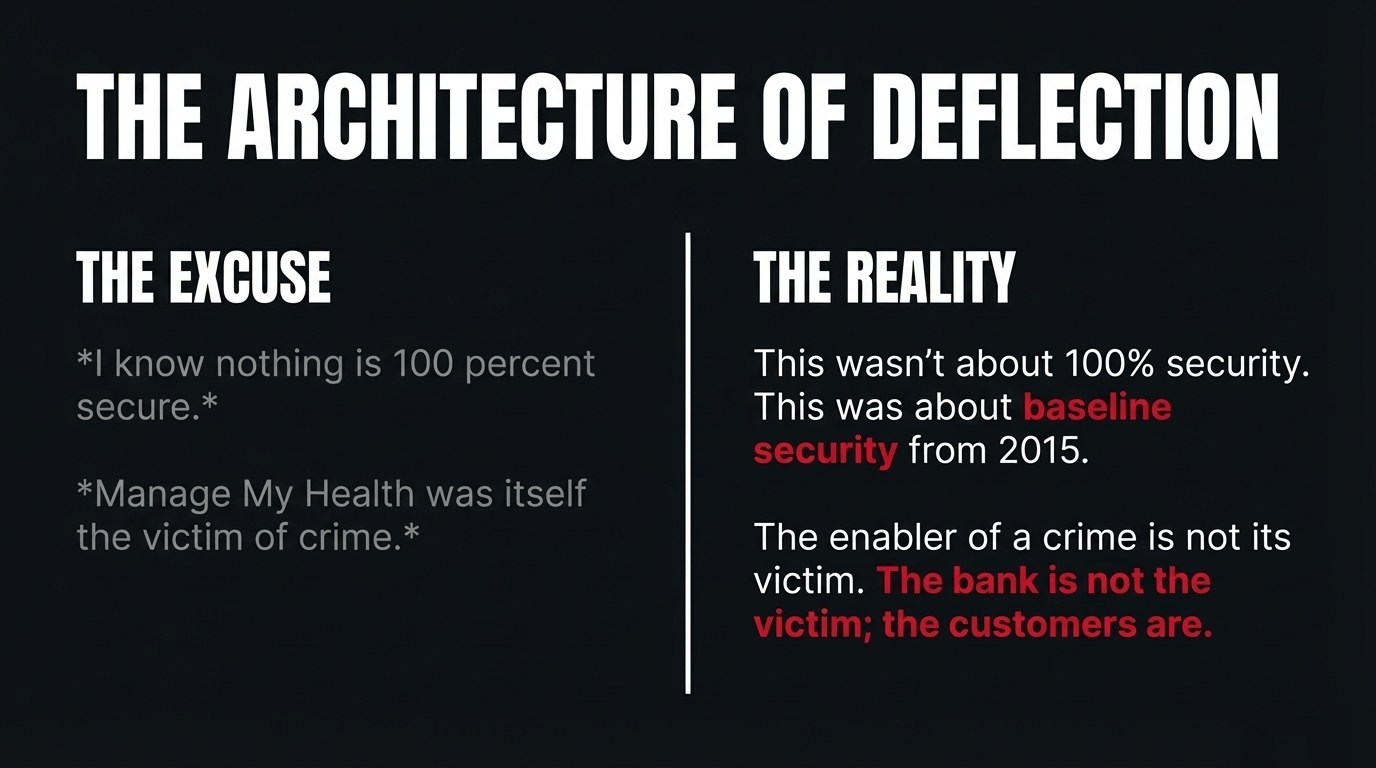
When RNZ pressed him on whether ManageMyHealth’s claims of being “secure” were accurate, Ramayah deployed the classic corporate deflection:
Translation: You can’t expect absolute security, so don’t blame us for basic failures.
But this is false. Healthcare data doesn’t require “100% security.” It requires baseline security. It requires the security measures that were standard in 2015. It requires multi-factor authentication, which has been considered essential since the mid-2010s.
ManageMyHealth doesn’t have “imperfect security.” ManageMyHealth has broken security. Negligent security. Preventable-breach security.
The Ransom Deadline Extended (Again): “5am Friday”
Here’s where things become truly revealing. When RNZ asked about the ransom deadline, Ramayah revealed that it had been moved:
New deadline: Friday, January 10, 2026, 5:00am NZDT.
But notice what he also revealed: “which we are monitoring.”
ManageMyHealth is watching the dark web. They’re tracking criminal communications. They know where their data is. They know what the hackers are saying about them.
Yet victims still don’t know:
- Exactly how many files were stolen
- Which specific health conditions were exposed
- Whether their data is being sold to identity theft networks
- What ManageMyHealth intends to do if the deadline is missed
The Refusal to Answer About Negotiations
The most revealing moment came when RNZ pressed Ramayah on whether ManageMyHealth was negotiating with hackers or considering paying the ransom:
RNZ: Has ManageMyHealth discussed paying the ransom internally?
RNZ: Asked again.
Ramayah: “As I have said here, I’m not going to comment on that.”
RNZ: Are you in negotiations with the people who took the data?
What Ramayah did NOT say: “We categorically will not pay ransom. We will not negotiate with criminals.”
What Ramayah DID say: Complete refusal to address the question.
This silence is deafening. In crisis management, refusing to deny something is equivalent to admitting it. If ManageMyHealth had no intention of negotiating, Ramayah would have said so clearly.
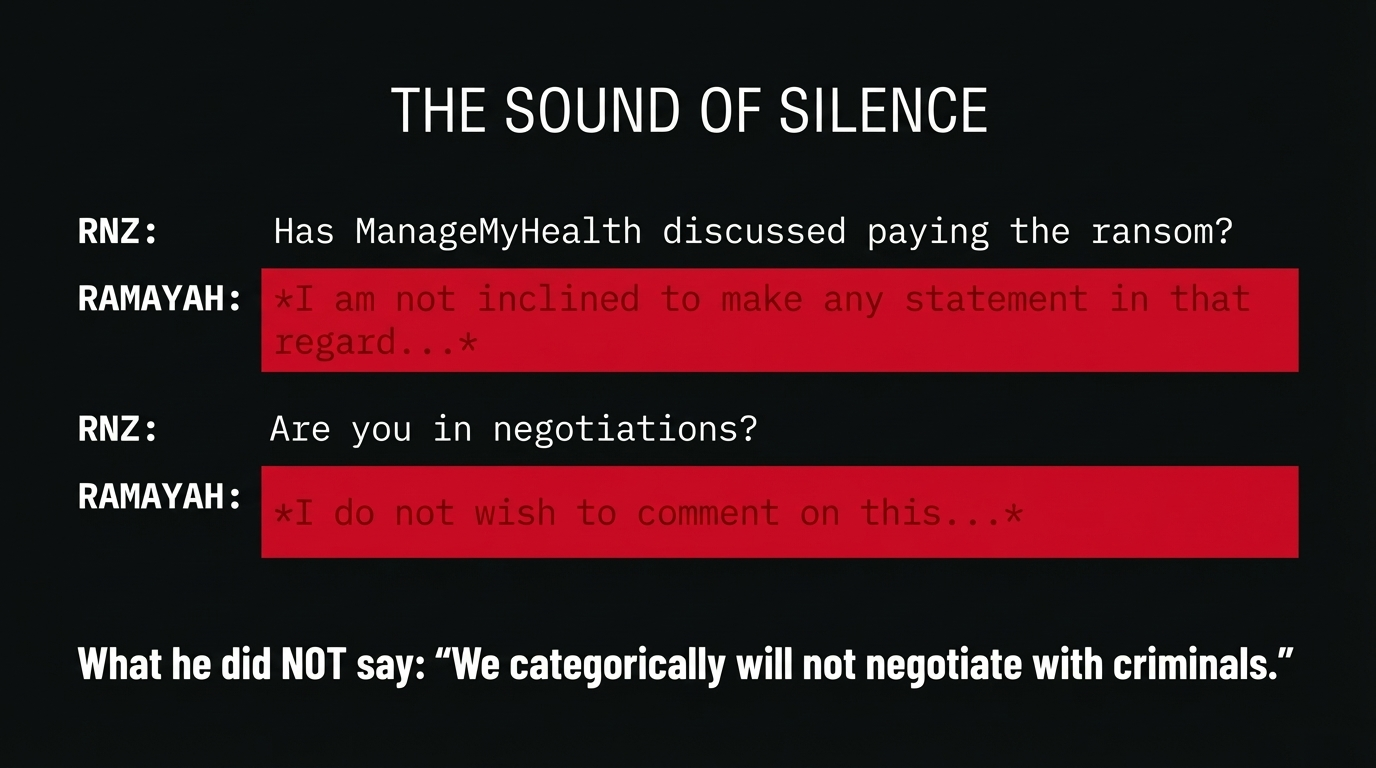
Instead, he stonewalled.
Playing the Victim: “ManageMyHealth Itself Is a Victim of Crime”
Perhaps the most audacious move in Ramayah’s interview was when he claimed:
“Ramayah said Manage My Health was itself the victim of crime.”
This is gaslighting.
Yes, a crime occurred. But the enabler of the crime is not its victim.
When a bank fails to install security cameras and gets robbed, the bank is not the victim. The customers are the victims. The bank is negligent.
ManageMyHealth:
- Failed to implement multi-factor authentication
- Failed to implement intrusion detection
- Failed to implement the most basic security measures
- Operated a health portal containing 126,000 people’s most intimate data without the security standards of a normal web application
ManageMyHealth is not a victim. ManageMyHealth is the negligent party.
The victims are the 126,000 people whose HIV status, mental health diagnoses, genetic test results, and medical photos are now on the dark web—because ManageMyHealth couldn’t be bothered to implement a password security system that was standard in 2010.
The Personal Appeal: “I’m Deeply Distressed”
Ramayah then deployed emotional rhetoric:
This is emotional manipulation designed to reframe the narrative: Look, I’m a victim too. We’re all in this together.
But you’re not in it together.
Ramayah owns the parent company (Cereus Health) that owns ManageMyHealth. He founded Medtech, the integration software that feeds data TO ManageMyHealth. He controlled every layer of the system that failed.
His personal distress does not absolve his corporate negligence. His shared victimhood does not change the fact that he, as CEO, failed to implement basic security.
This is a manipulation tactic: Use shared suffering to create emotional connection, then leverage that connection to bypass accountability.
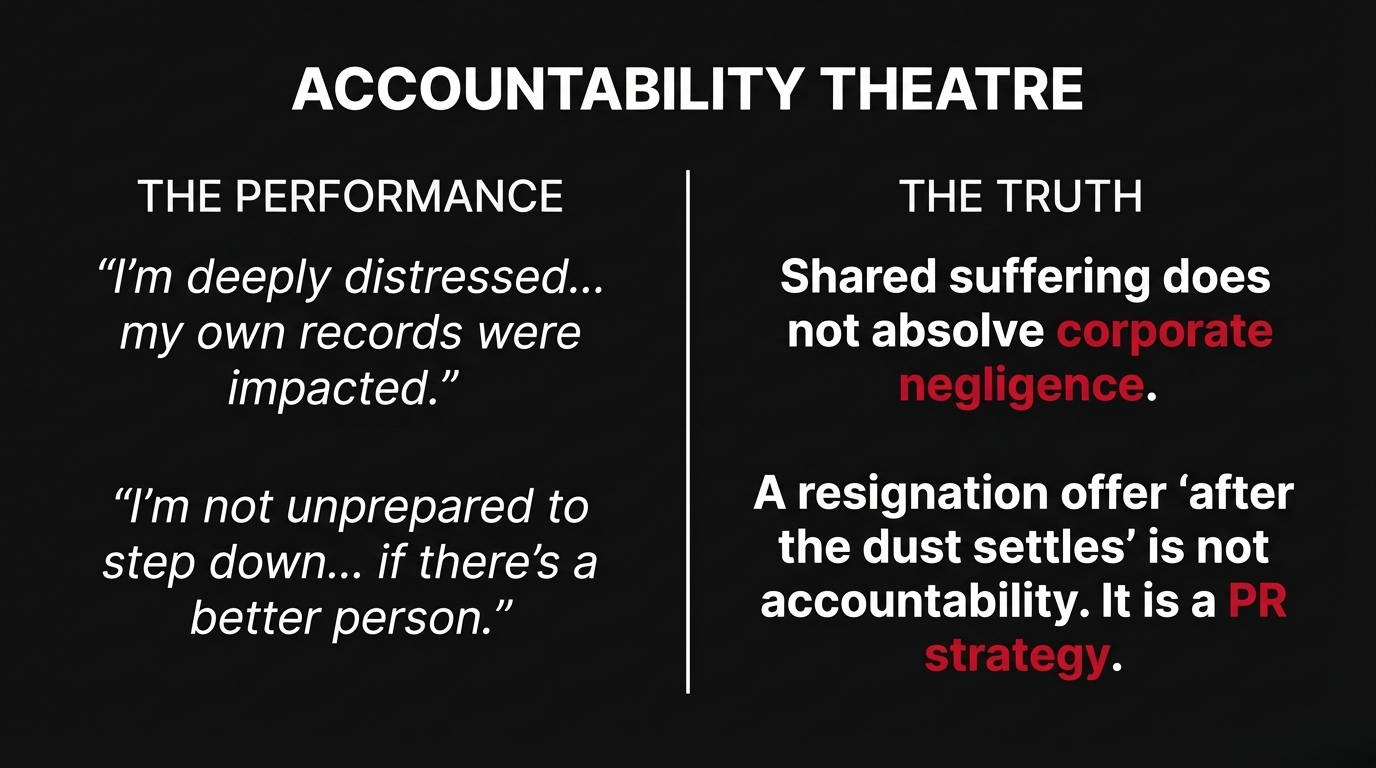
It won’t work on victims who’ve had their lives exposed.
“Since 2008, We Have Never Had a Breach”
“Since 2008 we have never had a breach of this nature.”
This proves nothing. Many breaches go undetected for months or years. The healthcare industry is plagued with breaches that organizations discover years after the fact.
Saying “we’ve never been breached before” after suffering a massive breach is meaningless. It either means you were lucky, or you didn’t notice.
Ramayah also admitted: “There’s no software in the world which is completely non vulnerable.”
But that’s not the excuse he thinks it is. Yes, all software has vulnerabilities. But basic authentication vulnerabilities—the kind that can be exploited with just a password—are not inevitable. They are negligent.
The Performative Resignation Offer: “I’m Not Unprepared to Step Down”
Finally, Ramayah suggested he might resign:
Notice the language:
- “After the dust settles” = Only when media attention fades
- “If there’s a better person” = Setting an impossible standard (anyone would be better)
- “Not unprepared” = Not committed, but open to the idea
This is not accountability. This is theatre.
If Ramayah had integrity, he would resign immediately. Instead, he’s signaling willingness to resign only if public pressure becomes unbearable, and only if someone better can be found.
The Whakapapa of Ramayah’s Control and Failure
To understand how one man’s negligence affected 126,000 people, you need to understand Ramayah’s role across the ecosystem:
The Ownership Structure
From utf9k.net investigation:
- Ramayah founded Medtech Global (integration software)
- Sold Medtech Global, then spun out ManageMyHealth into Cereus Health Group
- Ramayah is sole owner of Cereus Health
- Ramayah is CEO of ManageMyHealth
He owns it. He runs it. He built every layer of it.
The Security Failure Whakapapa
This is not a single point of failure. This is systemic negligence:
Layer 1: Medtech (integration software)
- Developed “on a tight budget” (per Reddit IT professionals)
- Used “outsourced labor from one of the CEO’s other ventures”
- Development team of “fewer than twelve individuals”
Layer 2: ManageMyHealth (portal)
- Deployed to clinics without “substantial security knowledge”
- No Chief Information Security Officer (CISO) role found
- No IT Security Manager found
- Apparently no security certifications among leadership
- No annual penetration testing mentioned
Layer 3: Data governance
- Patients enrolled without consent
- Data uploaded without patient knowledge
- No security baseline established
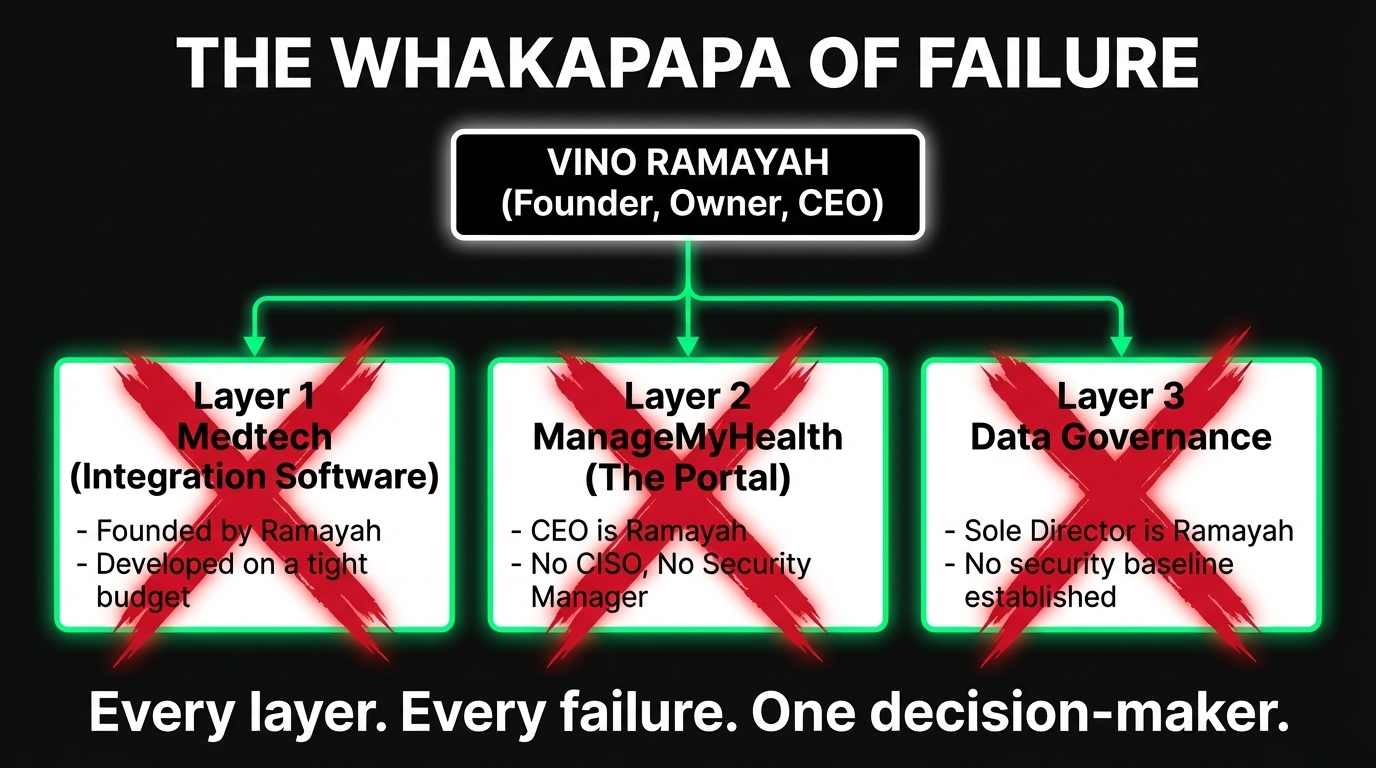
Every layer. Every failure. Traceable to a single decision-maker.
The High Court Injunction: Theatre of Legal Action
ManageMyHealth obtained a High Court injunction from Justice Andru Isac preventing “third parties from accessing the stolen data.”
This injunction is legally worthless for protecting victims:
- Dark web distribution can’t be stopped by injunction. Once data is distributed peer-to-peer, no court order stops its circulation.
- Takedown notices don’t work on criminal networks. ManageMyHealth is preparing to issue “takedown notices,” but hackers on the dark web don’t respond to legal threats.
- The injunction is about limiting corporate liability, not protecting victims. It creates a paper trail showing ManageMyHealth “tried to contain the damage”—useful in future litigation, but useless to victims.
The injunction covers approximately 430,000 documents with “highly sensitive and confidential information,” including “discharge summaries, referrals, personal health information uploaded by patients and other documents.”

But the injunction doesn’t prevent damage that’s already occurred. The data is already stolen. The injunction just prevents further public disclosure—which is performance, not protection.
What the CEO Interview Reveals: The Architecture of Negligence
Ramayah’s interview, in its totality, reveals this:
- The breach was preventable. (”Came in through the front door” = password-only authentication)
- ManageMyHealth knew it failed. (”Dropped the ball” = admitted negligence)
- The company is monitoring the dark web. (They know where their data is)
- Ramayah won’t confirm he won’t pay ransom. (Suggesting negotiations may be ongoing)
- ManageMyHealth claims victimhood. (Deflecting responsibility)
- Ramayah will only resign if forced. (No moral accountability)
This is not a company that was overwhelmed by sophisticated attackers. This is a company that chose not to invest in basic security, then got caught.
The Moral Clarity: Who Ramayah Is
Vino Ramayah:
- Founded the integration system (Medtech)
- Owns the parent company (Cereus Health)
- Ran the breached platform (ManageMyHealth)
- Failed to implement multi-factor authentication
- Failed to implement intrusion detection
- Failed to implement the security standards that were basic in 2015
- Admitted he “dropped the ball”
- Refuses to say whether he’s negotiating with criminals
- Plays the victim
- Uses emotional appeals to bypass accountability
- Offers performative resignation
This is not incompetence. This is negligence rising to the level of recklessness.
Under New Zealand’s zero-penalty regime, Ramayah faces zero consequences for failing to protect 126,000 people’s most intimate health data.
The Friday Deadline: What Happens Next
The new ransom deadline is Friday, January 10, 2026, at 5:00am NZDT.
If the deadline passes without further data release:
- Victims won’t be safer. The data is already circulating on the dark web.
- Ramayah won’t resign. He’s only willing “after the dust settles.”
- Security improvements won’t be implemented. The review starts January 30.
- Accountability won’t be pursued. There are zero penalties in NZ law.
The system will have succeeded in protecting the guilty while abandoning the victims.
The Question for Whānau
As we approach Friday’s deadline, ask yourself:
If a CEO admits his company “dropped the ball” on security, refuses to commit to not negotiating with criminals, plays the victim, and only offers to resign after media attention fades—what does accountability actually look like in Aotearoa?
Because Vino Ramayah’s interview just showed us: It looks like nothing.
Kia Kaha, Whānau
The ransom deadline approaches. Ramayah is monitoring the dark web. ManageMyHealth is preparing takedown notices. Brown is delaying his review for 30 days.
But 126,000 people are still waiting for:
- Direct notification
- Crisis support
- Credit monitoring
- Compensation
- Justice
Not after the dust settles. NOW.
Kia kaha. Keep demanding accountability. Keep naming those responsible. Keep refusing to accept that “we dropped the ball” is enough.
Because when a CEO admits negligence and then asks for trust, that’s when you know the system has completely failed.

Ivor Jones The Māori Green Lantern Fighting Misinformation And Disinformation From The Far Right